It is a long-standing joke that if you do a web search on any medical symptom, it will always lead to a web diagnosis of cancer. In the same manner, searching for any computer problem will always lead you to conclude that you have a nasty computer virus. Chances are you have never had, and never will have a computer virus, as this handy Venn diagram from XKCD.com demonstrates:
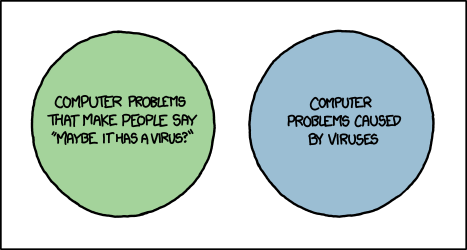
Now perhaps I’m being a bit nit-picky about the connotation of the term “virus” but there is quite a bit of misinformation and FUD (Fear, Uncertainty and Doubt) out there when it comes to computer viruses. Wikipedia defines a computer virus as “a malware program that, when executed, replicates by inserting copies of itself (possibly modified) into other computer programs, data files, or the boot sector of the hard drive.” The key here is that a virus spreads via various methods of replication – infecting other files. The vast majority of malware does not do this, and a virus is not going to change your home page, display pop-up ads, or install a toolbar as adware or Potentially Unwanted Applications (PUAs) may do. Your printer issues are not being caused by a virus either.
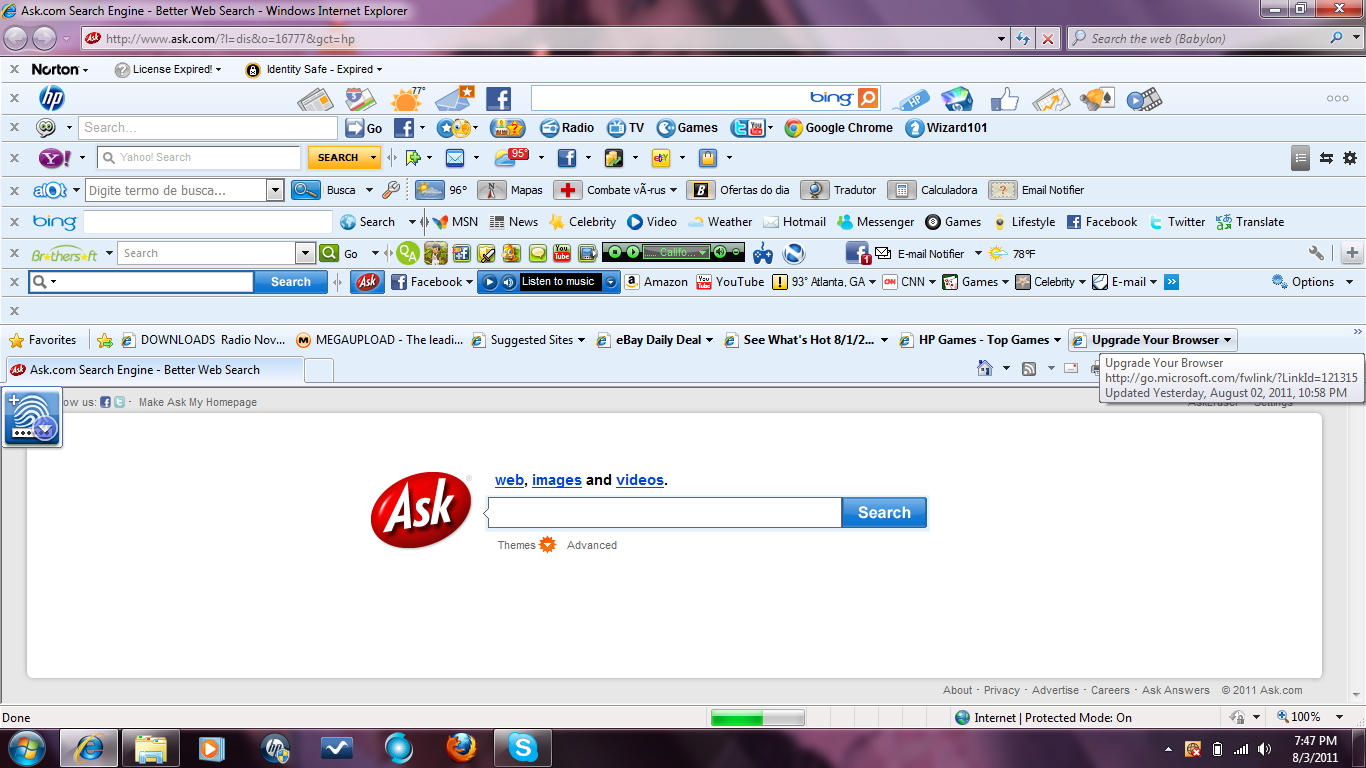
If you search for the name of any browser redirect, toolbar, pop-up ad, or any number of other computer problems you will almost always end up on a web page that claims the issue is due to a virus. These pages are rarely from reputable security vendors, and are often security blogs that feature prominent advertising for various legitimate and not-so-legitimate security software. The term “virus” is used to make you think the problem is far worse than it actually is in hopes that you will purchase the advertised security programs. These tactics are similar to those used by Rogue Security Software and tech support scams.
If you are searching for more information on a computer problem, pay attention to the sites that come up in the results, and to the terminology used. If the term “virus” comes up, chances are that the result is not from a trusted security company or computer support forum. There are several general computer support forums out there which offer excellent free support for general computing issues. For issues related to specific programs or hardware, most companies have their own support forums these days, and in many cases someone else has experienced the same issue that you are having.













 1982 – The first threat that occurred was the Elk Cloner (this however did not actually affect the Mac) which would cause the Apple II to boot up with a poem:
1982 – The first threat that occurred was the Elk Cloner (this however did not actually affect the Mac) which would cause the Apple II to boot up with a poem: 2004– Amphimix a program which is also a MP3 file. When launched it displays a dialog box which reads “Yep, this is an application. (So what is your iTunes playing now?)” It then loads itself into iTunes as an MP3 file called “Wild Laugh”, playing four seconds laughter.
2004– Amphimix a program which is also a MP3 file. When launched it displays a dialog box which reads “Yep, this is an application. (So what is your iTunes playing now?)” It then loads itself into iTunes as an MP3 file called “Wild Laugh”, playing four seconds laughter.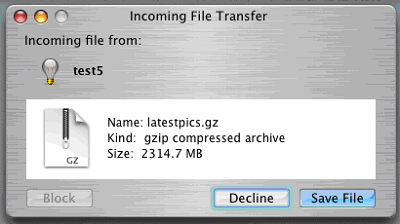 2006 – Leap is widely considered to be the original Mac Trojan. Leap used iChat to spread itself; forwarding itself as a latestpics.tgz file to the contacts on the machine. Inside the Gzipped Tar File (.tgz) was an executable file masked as a JPEG. When executed, it infected all Cocoa applications.
2006 – Leap is widely considered to be the original Mac Trojan. Leap used iChat to spread itself; forwarding itself as a latestpics.tgz file to the contacts on the machine. Inside the Gzipped Tar File (.tgz) was an executable file masked as a JPEG. When executed, it infected all Cocoa applications.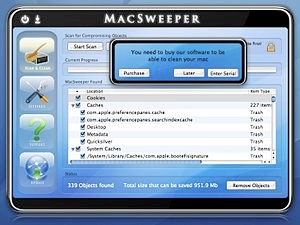 2008 – MacSweeper, Mac’s first ‘rogue’ application (a fake antivirus misleading users by reporting infections that doesn’t exists). When the infected user tried to remove the “infections”, MacSweeper asked to provide credit card details and pay $39.99 for a “lifetime subscription serial key.”
2008 – MacSweeper, Mac’s first ‘rogue’ application (a fake antivirus misleading users by reporting infections that doesn’t exists). When the infected user tried to remove the “infections”, MacSweeper asked to provide credit card details and pay $39.99 for a “lifetime subscription serial key.” 2011/2012 – Flashback was disguised as a Flash player download and targets a Java vulnerability on Mac OS X. The system is infected after the user is redirected to a compromised bogus site, where JavaScript code causes an applet containing an exploit to load. The Flashback malware was the largest attack to date, hitting more than 600,000 Mac computers.
2011/2012 – Flashback was disguised as a Flash player download and targets a Java vulnerability on Mac OS X. The system is infected after the user is redirected to a compromised bogus site, where JavaScript code causes an applet containing an exploit to load. The Flashback malware was the largest attack to date, hitting more than 600,000 Mac computers.