Social Nets Put Your Privacy at Risk
By Mike Kronenberg
 Attention Facebook and Twitter users: You’re still at risk. Last year, our survey found that lots of people using social networking sites were taking the risk of financial loss, identity theft, and malware infection. Have things gotten any better? Well, the answer is yes but, unfortunately, not better enough — and potentially a lot worse for some of you.
Attention Facebook and Twitter users: You’re still at risk. Last year, our survey found that lots of people using social networking sites were taking the risk of financial loss, identity theft, and malware infection. Have things gotten any better? Well, the answer is yes but, unfortunately, not better enough — and potentially a lot worse for some of you.
The results of our 2010 survey reveals that more of you are adhering to some safe behaviors — like blocking profiles from being visible through public search engines. That’s a good thing, but the downside is over 25 percent of you haven’t changed your default privacy settings. And more that three quarters of survey respondents haven’t placed any restrictions on who can see their recent activity.
I worry about this because you can’t escape the fact that rogue operators are always trying to extract details about you. They want access to anything that can help them dig into your private life. They can break into Web mail accounts, get your credit card number, steal your identity, or even attack you through cyber-stalking.
And they’ll do anything to get the info, from attacking you with malware to tricking you into revealing passwords.
With that, and our survey in mind, on the following page I’ve posted a few suggestions you can follow to protect yourself.
Pushu Variant Spams Hotmail, Cracks Audio Captchas
 A new version of Trojan-Pushu is doing some interesting stuff to bypass captchas used by Microsoft’s Hotmail/Live.com/MSN webmail services in order to spam people with links to malicious Yahoo Groups pages.
A new version of Trojan-Pushu is doing some interesting stuff to bypass captchas used by Microsoft’s Hotmail/Live.com/MSN webmail services in order to spam people with links to malicious Yahoo Groups pages.
The three-year-old spy (known by a variety of other aliases, including Cutwail, Pushdo, Diehard, and Rabbit) has always been, primarily, a spam bot. In this case, however, the spy is not sending spam by connecting to open mail relays or more traditional means; It’s spamming through the Hotmail/Live.com Web mail interface. Most interestingly, during the course of the spam sessions, the spy apparently pulls down “audio captchas” and successfully sends back the correct response, which permits it to continue spamming.
Audio captchas are just what they sound like they are: A voice, often female, reads a sequence of 10 numbers in an artificially noisy background. The purpose is simple: to ensure that a human being, and not some automated process, is entering data into a form. Just as you would type in the scrambled-up letters from a captcha image to proceed, with an audio captcha you have to type the correct numbers from the recording, or the site won’t let you continue.
That doesn’t seem to be a problem for this Pushu variant. We’ve seen Trojans attempt to crack visual captchas a number of ways, including using optical character recognition; employing a mechanical turk service (where humans are paid fractions of a penny for each correctly entered captcha); or by prompting the victim him- or herself to enter captcha text, disguising the captcha form as some sort of Windows prompt. This is the first time I’ve heard of a Trojan attempt to crack the audio captcha, let alone succeed.
Weird New Koobface URLs Use Old Tricks
 Pretty much since it arrived on the malware scene, Koobface has used the technique of sending messages with Web links — in your name, to your friends — as a method of propagating the infection to others. Using your name is a powerful social engineering trick, and the makers of the worm have tried innumerable ways to mask the danger behind those dangerous links: They’ve used “short link” services like Bit.ly to hide the destination; They build pages on sites normally considered safe, like Blogspot or Google Reader, that simply redirect users to a dangerous page; and they use stolen credentials for the Web servers of legitimate businesses to upload their own malicious content there.
Pretty much since it arrived on the malware scene, Koobface has used the technique of sending messages with Web links — in your name, to your friends — as a method of propagating the infection to others. Using your name is a powerful social engineering trick, and the makers of the worm have tried innumerable ways to mask the danger behind those dangerous links: They’ve used “short link” services like Bit.ly to hide the destination; They build pages on sites normally considered safe, like Blogspot or Google Reader, that simply redirect users to a dangerous page; and they use stolen credentials for the Web servers of legitimate businesses to upload their own malicious content there.
Since February, Koobface has tried another technique: It has used different URL encoding schemes, which many browsers but few humans can interpret. You click an odd-looking link and before you know it, you’re on a site that’s trying to push an infection at your PC.
This “new” trick actually harkens back to 2001, when spammers were using so-called dotless IP address tricks to bypass security features in Internet Explorer. A Windows patch issued in October of that year fixed the bug in IE that gave dotless IP addresses additional security permissions. But the IE, Firefox, and other browsers remain capable of taking a URL in the form of (for example) http://1078900434 and correctly translating to a standard IP address, then loading, the page hosted at the IP address that number represents. (The dotless link above will take you to Webroot’s Web site.)
Fakealert Accurately Mimics Windows Update
 A new Windows Update-themed stupid malware trick that’s making the rounds appears to be trying to capitalize on the recent frequency of “out of band” Windows patches Microsoft has been releasing lately.
A new Windows Update-themed stupid malware trick that’s making the rounds appears to be trying to capitalize on the recent frequency of “out of band” Windows patches Microsoft has been releasing lately.
The spy, which serves as nothing more than a vehicle for the fraudulent sale of a fake product called Antimalware Defender, so closely resembles a Windows Update installation dialog that some members of our threat research team who saw these files had to pause and look carefully at the dialog box before deciding it is, in fact, a big fat hoax. Even the Microsoft Knowledge Base article the dialog box references is a real KB article…though it has nothing to do with security.
 The entire scam is facilitated through a nearly-1MB DLL file, which contains all the instructions required to display the fake popups from the System Tray, the fake Windows Update dialog box, and the fake antivirus “scan” window which appears when you play along with the app. The DLL appears when you visit certain Websites that push drive-by downloads at visitors.
The entire scam is facilitated through a nearly-1MB DLL file, which contains all the instructions required to display the fake popups from the System Tray, the fake Windows Update dialog box, and the fake antivirus “scan” window which appears when you play along with the app. The DLL appears when you visit certain Websites that push drive-by downloads at visitors.
Botnet Trojan Adds “Gootkit” Code to Web Pages
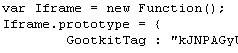 An insidious new Trojan that finds its way onto Windows PCs in the course of a drive-by infection employs a novel method to propagate: It connects to Web servers using stolen FTP credentials, and if successful, modifies any HTML and PHP files with extra code. The code opens an iFrame pointing to a page that loads browser exploits. The exploit pushes down the infection, which then perpetuates the process. The initial infection vector in this case was a spam message supposedly from Amazon.com containing a link to the page which performs the drive-by attacks.
An insidious new Trojan that finds its way onto Windows PCs in the course of a drive-by infection employs a novel method to propagate: It connects to Web servers using stolen FTP credentials, and if successful, modifies any HTML and PHP files with extra code. The code opens an iFrame pointing to a page that loads browser exploits. The exploit pushes down the infection, which then perpetuates the process. The initial infection vector in this case was a spam message supposedly from Amazon.com containing a link to the page which performs the drive-by attacks.
The malware, which we’re calling Trojan-Backdoor-Protard, appears to seek out Web servers for which the FTP credentials may have been previously stolen in an earlier attack. Those servers all contain a pair of benign HTML tags that appears to be long strings of gibberish characters.
Code within the scripts this spy uses indicate the malware’s creators are calling the server modifications a Gootkit, and the gibberish embedded in the files Gootkit Tags. The Trojan also loads itself on an infected machine using a registry key, naming the service that loads either “kgootkit” or “gootkitsso.” During the course of researching the malware, we observed the Trojan modify these pages such that the Trojan inserted the malicious code between the two Gootkit Tags.
It stands to reason that, if you find these so-called Gootkit Tags embedded within files on your own Web server, you can be fairly confident that an FTP password has been compromised, and all your FTP passwords should be changed immediately.
Twitter Phish Floods Network with Short URLs
 All day, I’ve been getting reports from my Twitter-using friends and acquaintances that they’ve been receiving tweets of short URLs. I took a look and it looks like another phishing campaign aimed at users of the social network is underway. The short URLs, prefaced with the message “This you???” lead to a fake Twitter login page.
All day, I’ve been getting reports from my Twitter-using friends and acquaintances that they’ve been receiving tweets of short URLs. I took a look and it looks like another phishing campaign aimed at users of the social network is underway. The short URLs, prefaced with the message “This you???” lead to a fake Twitter login page.
The fake login page is hosted on a domain that points to a server in China. Other domains that are currently hosted on that same server’s IP address, including bzpharma.net, have previously been implicated in earlier Twitter spam campaigns. The same domain appears to also be attempting to phish credentials to AOL’s Bebo social network, and has reportedly begun spamming users with fake pharma ads.
It appears a lot of people may get tripped up in the rush to see what the link is all about. After you type anything at all into the phishing version of the Twitter login form, your browser is redirected to a hastily created, empty blog page on Blogspot. Meanwhile, the tweets keep on coming.
Just a reminder to our Twitter fans: Please look at the address bar before you enter your Twitter credentials. As you can see from the screenshot above, it’s painfully obvious that this is not the legitimate twitter.com URL.
New Research: IT Pros Sound Off On 2010 Security Concerns
Research from the enterprise security experts at Webroot
With the explosion of social networking sites like Twitter and Facebook in 2009, it’s no surprise cybercriminals have set their sights on these Web sites for new victims. Facebook now has over 400 million active users and Twitter has over six million — a sizeable pool of potential targets.
These new threats are a cause of great concern for IT managers and businesses. Webroot recently surveyed over 800 IT professionals in the US, UK and Australia, at companies ranging from 100 to 500 people in size, to learn what are their biggest concerns for 2010. Eighty percent of those who responded anticipate Web 2.0-based malware threats will be among their biggest challenges, and 73% said these types of malware are much harder to manage than email-based threats.
Many IT admins reported they thought their organizations were sufficiently protected, but that wasn’t always the case: Significant numbers reported attacks from viruses (60%), spyware (57%), phishing attacks (47%), hacking attacks (35%), and SQL injections of their Web sites (32%). What’s more, because malicious hackers have a financial motive, individuals who possess sensitive business data are perfect targets. Increasingly, small and medium-sized businesses (SMBs) come under attack because they are less likely to have the multiple layers of protection that larger enterprises do.
Data breaches, when they happen, can be devastating to SMBs: According the the FBI, blended Web and email attacks led to approximately $100 million in attempted losses last year. SMBs can take precautions to make sure they aren’t a part of these staggering statistics. It is important to keep up with the latest threat vectors by using a security service with URL filtering, end user policy management and virus protection, and by making sure employees are educated on know to avoid threats in a growing landscape — especially when it comes to social media.
Webroot will address this topic in greater depth when our CTO Gerhard Eschelbeck delivers a Web security trend report at the RSA Conference 2010 Wednesday, March 3, at 4:30 p.m. PST in the Briefing Center on the Expo Hall floor. We’ll continue the conversation at Infosec Wednesday, April 28 at 3:20 p.m. GMT in Earls Court when Eschelbeck presents Securing the Internet for a Web 2.0 Collaborative Culture.
Phishing Campaign Targets Frequent Fliers
 A variation of a phishing scam aimed at members of American Airlines’ AAdvantage program is circulating again. With links to a phishing Web site embedded in a spam message, the scampaign promises (in characteristically broken English) that all participants in a survey will receive, depending on the campaign, either $100, or “$50 & 25,000 miles” credited to their account.
A variation of a phishing scam aimed at members of American Airlines’ AAdvantage program is circulating again. With links to a phishing Web site embedded in a spam message, the scampaign promises (in characteristically broken English) that all participants in a survey will receive, depending on the campaign, either $100, or “$50 & 25,000 miles” credited to their account.
The spam messages are appearing not only in email inboxes, but also as posts on what appear to be compromised blogs. The messages usually include the following text, signed by “American Airlines Reward Department,” obvious errors and all:
We are proud to inform you that today (current date) AmericanAirlines.com launch a new reward program. Please log in to your American Airlines account and take the 5 questions survey. For your effort you will be rewarded with …
It’s also amusing to note that the fraudsters have had to periodically raise the bar on what they’re offering. In the earliest iterations of this scheme, dating back to autumn 2008, they only offered $50…no miles included. Even in this tough economy, a fraudulent offer of merely $50 isn’t good enough to snare dupes anymore. Suckers Customers can be so demanding!
British Music Awards Draws Web Scams
 Music fans may already be aware that next Tuesday the British music industry will honor the top acts of the year at a ceremony known simply as The BRITs. What they may not know is that common Internet criminals have begun to target people searching for information about the artists and the music connected with the awards for attack.
Music fans may already be aware that next Tuesday the British music industry will honor the top acts of the year at a ceremony known simply as The BRITs. What they may not know is that common Internet criminals have begun to target people searching for information about the artists and the music connected with the awards for attack.
This will be the 30th ceremony held in the 33 year history of the awards. As in previous years, the BRIT Trust (a charity run by BPI, the UK’s recording industry trade association) will donate profits from the ceremony, including the sale of a three-CD compilation, to various charities that benefit young people in the UK.
Unfortunately, at least two distinct threats face Web surfing Anglo-musicophiles: Bogus music download sites, which tease users with offers of “free downloads” of the compilation set, but then require users to register and pay a fee — none of which ends up in the hands of the BRIT Trust charity; And the purveyors of irritating fake alert messages, which invariably lead to rogue antivirus downloads, are also heavily pushing themselves to near the top rankings in some search results.
Tax-Themed Phishing Scams Cross More National Borders
 Sometimes, the early bird gets the worm — and not in a good way. People who file their tax returns early are being targeted by a phishing scam that comes with the promise of a big income tax refund.
Sometimes, the early bird gets the worm — and not in a good way. People who file their tax returns early are being targeted by a phishing scam that comes with the promise of a big income tax refund.
Unlike previous tax-themed scams, which have been based on the stick — fake warnings or penalties supposedly issued by the Internal Revenue Service and its UK counterpart the HMRC — these carrot Tax Refund Online Form frauds promising payouts appear to originate from different countries’ tax authorities, notably those of India and Canada.
We’ve come across a number of identical pages that have been cleverly designed to resemble the appearance of the Web sites of India’s Income Tax Department and the Canada Revenue Agency (CRA). The fake CRA “Tax refund online form” claims that the recipient will receive CAN$386 — a nontrivial sum — if they provide the necessary credit card information in the form. Wait, what?
The fake page supposedly from India (which inexplicably refers to the Indian Ministry of Finance as the IRS) tells prospective victims that they stand to gain a whopping 820.50 rupees for filling out a form with not only full credit card details but also a bank account and routing number, and debit card PIN, then waiting two to three business days for the information to be “processed” or, as we call it in this country, “stolen, used to commit fraudulent purchases, then discarded.”
And yes, you read that right — 820.50 rupees. For those unfamiliar with current rupee-to-dollar exchange rates, at a little over 46 rupees to the dollar, that’s a false promise you will receive…wait for it…nearly eighteen US dollars.
News flash, income tax filers: If you have been following the law and filing tax returns, and your respective government wants to issue you a refund, they already know where your bank accounts are.
read more…
Play it Safe on Safer Internet Day
 February 9 marks Safer Internet Day, and around the world, people are trying to help their fellow netizens navigate an obstacle course of threats to their security and privacy. InSafe, the organization funded by the EU that sponsors the annual youth-targeted event, has themed the day around the concept “Think B4 U post.” As grammatically sloppy as that sounds, it’s actually good advice.
February 9 marks Safer Internet Day, and around the world, people are trying to help their fellow netizens navigate an obstacle course of threats to their security and privacy. InSafe, the organization funded by the EU that sponsors the annual youth-targeted event, has themed the day around the concept “Think B4 U post.” As grammatically sloppy as that sounds, it’s actually good advice.
Readers of this blog shouldn’t be surprised that myriad dangers threaten the safety of all Internet users: Keylogging software disguised as “updates” are everywhere; Fake security alerts pop up when you least expect them; Phishing Web pages are more cleverly designed than ever to steal your passwords; Spam is choking email; Worms stalk social networks; Even your mobile phone is at risk of malicious software designed to steal valuable information from you. The big question on everyone’s mind is: What do you do to protect yourself?
[vimeo 9266107]
The answer’s simple, really. You have to think before you act, and make sure you understand the consequences of whatever you do, write, post, or click online. Once you develop your Internet spidey senses, you’ll be able to spot something that’s out of place, or weird, or just dodgy before it catches you out.
Despite the increasingly clever tricks criminals employ, they still have to lie and cheat in order to steal. What follows are a few easy ways you can catch them out in their lie before it’s too late. We’ve also put together a short video that shows just how easy it is, once you’re in the right frame of mind.
read more…
Massive Spam Campaign Impersonates Social Networks
 Spammers are the source of a flood of messages that appear to originate from various social networks, including Facebook and Myspace, as well as popular sites like iTunes.
Spammers are the source of a flood of messages that appear to originate from various social networks, including Facebook and Myspace, as well as popular sites like iTunes.
The spam messages usually just contain a link, and possibly a few words. Their subject matter falls into three general categories common to most contemporary spam: Pill vendors, Russian bride “vendors,” and drive-by download sites hosting Zbot password-stealer installers.
It’s not unusual for spammers to forge the return addresses, but the sheer volume of spam that has been forged so it appears to originate from MySpace, Facebook, or iTunes is notable.
















































































