10 Threats from 2010 We’d Prefer Remain History
 With 2010 finally behind us, and an unknown number of cyberattacks likely to come in the new year, I thought I’d run down a brief list of the malicious campaigns criminals pulled off last year that I’d really dread to see anyone repeat. Now that they’re in the past, they should stay there.
With 2010 finally behind us, and an unknown number of cyberattacks likely to come in the new year, I thought I’d run down a brief list of the malicious campaigns criminals pulled off last year that I’d really dread to see anyone repeat. Now that they’re in the past, they should stay there.
Operation Aurora: Google’s accusation (with Adobe, Juniper Networks, Rackspace, Yahoo! and Symantec) that China hacked its servers, allegedly stealing private emails stored on the company’s servers. The big surprise wasn’t that it was happening, but that companies were publicly talking about it.
Abused ccTLDs: 2010 saw lots more malicious content originating from previously un-abused country code top-level domains, which are assigned to national authorities, such as the .in (India) and .cc (Cocos (Keeling) Islands) top-level domains. The Cocos Islands’ .cc domain deserves particular note because the more than 2200 malicious domains (discovered during 2010) hosted under this ccTLD outnumber the approximately 600 human inhabitants of the tiny archipelago by nearly 4-to-1.
Koobface: “the little social network worm that could” employed new URL obfuscation techniques, introduced its own keylogger, and focused efforts on a smaller number of social media sites, while Facebook got more proactive at shutting down the worm’s operations quickly. Maybe this year they’ll disappear altogether.
Software Channels the Cloud – For the Better
By Ian Moyse, EMEA Channel Director
I continue to read doom and gloom news about the future of the software distribution channel, in particular, how it’s being impacted by the global recession, by catalogue providers, and most importantly, the cloud security delivery model. We already know that cloud software will change the security landscape as we know it today, and it looks likely to change the software marketplace as well.
In my opinion, this change is long needed, and for the better. Resellers who find the right education and support for transitioning to a mixed world with both traditional and cloud delivery mechanisms will find this a much-needed improvement.
The security landscape is constantly changing. With new attacks coming from far more sophisticated sources and in greater volumes than ever before, channel partners now have an unprecedented opportunity to help their customers protect themselves with cloud-based services, which are far more effective and easier to maintain than traditional, on-premises products.
But two potential roadblocks may stand in the way of progress: Many CIOs or IT administrators and other potential customers may not be well versed in the cloud, and they’ve likely become sensitive to budget constraints during the recession. Naturally, they tend to turn to a balance of price versus relationship and support.
Christmas IE Zero-Day Thwarted. Ho ho ho.
 Yesterday, two different 0 day exploits against Internet Explorer were published, just in time for the holidays when most of you (and many security researchers as well) are taking time off from work. The exploit, named CVE-2010-3971, is fairly serious, affecting the latest builds of IE versions 6 through 8.
Yesterday, two different 0 day exploits against Internet Explorer were published, just in time for the holidays when most of you (and many security researchers as well) are taking time off from work. The exploit, named CVE-2010-3971, is fairly serious, affecting the latest builds of IE versions 6 through 8.
Well, I’d normally get all hot and bothered about the fact that this kind of event might force some of our research team to spend their precious vacation time working the problem and coming up with a comprehensive solution. Normally, but not this time.
This time we headed the Black Hats off at the pass, and put a stop to these shenanigans before they started. Word from the Webroot Web Security Service team — the builders of our very slick cloud protection service for businesses — is that their Javascript heuristics engine is able to block any Web page that’s trying to use the exploits to try to take over your computer. The screenshot above shows what happened when we tried to browse to the proof-of-concept exploit page on a machine protected by the Web Security Service.
 Of course, that’s great for corporate folks, but what about our home users running Webroot Antivirus or Internet Security Essentials or Complete? Well, we block it there, too. If you happened to stumble upon a Web page with the exploit running inside it, you might see a popup like the screenshot here, which is just telling you that we’ve prevented the page containing the exploit from loading in your browser. For the people playing at home, please ensure that you’re running the latest version of your antivirus with the most current updates, with the File System Shield and the Execution Shield turned on (and turn Gamer Mode off while you’re surfing).
Of course, that’s great for corporate folks, but what about our home users running Webroot Antivirus or Internet Security Essentials or Complete? Well, we block it there, too. If you happened to stumble upon a Web page with the exploit running inside it, you might see a popup like the screenshot here, which is just telling you that we’ve prevented the page containing the exploit from loading in your browser. For the people playing at home, please ensure that you’re running the latest version of your antivirus with the most current updates, with the File System Shield and the Execution Shield turned on (and turn Gamer Mode off while you’re surfing).
So, tough luck exploit writer guys. Better luck next time. I know someone is getting a bigger lump of coal than usual in his stocking this year, and I can’t think of anybody who deserves it more.
Fake Firefox Update is a Social Engineering Triple Fail
![]() Where’s the work ethic, malware geniuses? If this latest example of shenanigans is the best you can deliver, you’re not even trying to generate convincing scams — or even something that makes sense — anymore.
Where’s the work ethic, malware geniuses? If this latest example of shenanigans is the best you can deliver, you’re not even trying to generate convincing scams — or even something that makes sense — anymore.
One of our Threat Research Analysts pointed me to a Web page hosting a fake update program for Firefox the other day, and the only thing it was useful for was a pretty good laugh.
In replicating the Firefox “you’re now running…” page, the malware distributor managed only to build something that looks remarkably similar to a more sophisticated, and ultimately more plausible, scam we first described this past summer. But the scam is full of fail.
The malicious page, which had been hosted at firefoxlife.cz.cc (and is now, thankfully, shut down), looks like the page that automatically pops up when you first launch the Firefox browser after you’ve applied an update. Ultimately, it not only fails the smell test, giving the user contradictory information, but also fails at the effective malware test, delivering multiple different samples, all of which crashed when we tried to run them on test systems or in debuggers.
read more…
Internet Misuse: Bandwidth Does Matter
By Ian Moyse, EMEA Channel Director
 Recent studies demonstrate that upwards of 25% of Internet bandwidth in an office are consumed by employees misusing the internet. According to Gartner, the average growth of business email volume is 30% annually, with the average size of the email content growing in parallel. Add to this the growth of Web misuse from streaming media, downloads, file sharing, social networking, and spam, and it becomes pretty clear that the mismanaged cost to business of non-work-related Internet use is already bad and getting worse.
Recent studies demonstrate that upwards of 25% of Internet bandwidth in an office are consumed by employees misusing the internet. According to Gartner, the average growth of business email volume is 30% annually, with the average size of the email content growing in parallel. Add to this the growth of Web misuse from streaming media, downloads, file sharing, social networking, and spam, and it becomes pretty clear that the mismanaged cost to business of non-work-related Internet use is already bad and getting worse.
There are plenty of examples, including employees wasting more than two hours a day on recreational computer activities (according to a survey fielded by AOL & Salary.com) and that, according to an IDC report, “30% – 40% of Internet use in the workplace is unrelated to business.”
Studies and surveys such as these typically focus only on lost productivity — and there’s no doubt that’s bad enough. But they rarely discuss the significant hidden financial impact of bandwidth wastage from these activities.
The Big Picture for 2011 Security Trends
By Gerhard Eschelbeck
 As 2010 winds down, I wanted to pull out the crystal ball and talk for a moment about where the security industry seems to be heading in the coming year, and where we anticipate threats and targets.
As 2010 winds down, I wanted to pull out the crystal ball and talk for a moment about where the security industry seems to be heading in the coming year, and where we anticipate threats and targets.
Mobile platforms: If you’re reading this, there’s a good chance you have either an iPhone, an Android phone, or a Blackberry in your pocket, case, or on your desk right now. If that’s true, then the data on that device is the next big target for criminals, and the newest front in the war on cybercrime. Users have embraced the advantages of mobile platforms, and even though IT admins may officially consider some or all of them “unsupported” in some organizations, you can’t abandon users who will choose convenience over strict IT policy. I predict that mobile platforms will continue to grow at a rapid pace, and we’ll soon reach the threshold level where malware creators start to take notice in significant numbers. IT admins should embrace these new platforms, and take steps to protect users who insist upon having them, even though doing so may make their work harder.
Social engineering: Whether you use a single PC at home, or manage a network of 25,000 laptops and desktops at work, social engineering scams have become so convincing that it’s a wonder IT admins ever get a good night’s rest.
It doesn’t matter how comprehensive your patch and update schedule is — when a sufficiently convincing spam email reaches a gullible employee, all bets are off. With targeted attacks becoming more common, the best defense against this threat continues to be education. Every user, from the newest administrative assistant to the C-level executives, needs training in identifying and avoiding fraudulent email and other messages, harmful file attachments, and Internet behavior that can lead to trouble.
Cloud vs. Desktop: We’ve seen demand for cloud-based services increasing across all segments of the business. In small and medium-sized businesses, we’re continuing to see strong demand for cloud-based solutions, and we expect that to continue next year. Overworked admins like the ease of administration and the performance benefits of cloud security services. And for the first time, we’re seeing consumers getting interested in the advantages the cloud brings to PC protection, including the speed that updates make it to the user of an infected computer.
At the larger end of the enterprise business segment, IT administrators must juggle the requirements of government regulations with the performance advantages that cloud services have to offer. In those cases where security regulations may not permit some kinds of data to move out into the wider Internet, we’ve seen a demand for what we call private cloud architecture — something that offers the performance benefits and features of a cloud solution, within an organization, while, at the same time, satisfying regulatory constraints on how companies move or store data.
We also can see how criminals have developed a taste for the vast volumes of sensitive data stored in the cloud, and anticipate that malware creators and other attackers will try to steal data stored in the cloud with increasing frequency.
Security Updates: More than 60 percent of malware attacks come from known vulnerabilities, so no matter whether you’re a one-person shop, or manage many thousands of desktops, maintaining not only the operating system but also the third party applications on which you (and your organization) depend should be a top priority. Besides office applications, attacks in the past year have focused on programs like Adobe Reader, Java, Flash, AutoCAD, media players, graphic design tools, and various browsers and browser plug-ins. IT departments should never let a new computer get to an employee that has anything older than the very latest build of these critical applications.
Consolidation: While not expressly a security trend, larger companies — some in the security space, and some that have not previously played there — have been augmenting their offerings. Intel’s purchase of McAfee, for example, appears to extend their platform beyond mere chipmaking. Other acquisitions, such as Webroot’s purchase of Brightcloud and Prevx, help companies acquire capabilities that can defend against, or remediate, a specific kind of threat. HP, IBM, and Symantec have done similar things, and with each acquisition, the companies gain another part of a toolkit they can use to respond to emerging threats. We expect to see more companies in this space merge and transform themselves over the next year.
Chinese Trojan Turns Infected PCs Into Web Servers
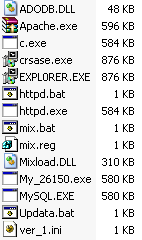 A complex and elaborately conceived family of malware that originates in China installs the Apache Web server, as well as half a dozen keylogger and downloader payloads, disguised as components of legitimate apps. We and a few other antivirus vendors are calling this type of malware Taobatuo.
A complex and elaborately conceived family of malware that originates in China installs the Apache Web server, as well as half a dozen keylogger and downloader payloads, disguised as components of legitimate apps. We and a few other antivirus vendors are calling this type of malware Taobatuo.
It just so happens that I’ve been setting up a Windows virtual machine with the latest versions of Apache, MySQL, and PHP for an unrelated project. I hadn’t installed these apps onto a Windows box before, and Apache in particular is notoriously finicky about Windows installations, so after several days of trial and error (mostly error) I was somewhat amused to discover, after finally getting Apache to work, that the malware sample I tested actually pulls down its own working, customized Apache installer…along with a bunch of phishing Trojans, keyloggers, and downloaders, all dressed up to look like the services you might see on a Microsoft-based Web server.
It just goes to show how much good these malware creators could accomplish, simply if they wanted to. But that’s clearly not the goal. The malware, along with text files containing instructions for the malware, came from taobao.lylwc.com. That’s not to be confused with Taobao.com, one of China’s most heavily trafficked Internet portals. This site and the real Taobao are not related in any way I can determine, other than the (ab)use of the Taobao name.
 The lylwc.com domain itself is quite a piece of work. It claims to offer free downloads or streams of current Hollywood movies, as well as an extensive library of films and TV shows. The operative word is “claims” — when you try to view those movies, the site attempts to push a download of a Trojaned installer for the QVOD media player (a streaming media app that’s popular in China). So let’s just say I wasn’t all that surprised to find the taobao subdomain of this Web site hosting a raft of malware.
The lylwc.com domain itself is quite a piece of work. It claims to offer free downloads or streams of current Hollywood movies, as well as an extensive library of films and TV shows. The operative word is “claims” — when you try to view those movies, the site attempts to push a download of a Trojaned installer for the QVOD media player (a streaming media app that’s popular in China). So let’s just say I wasn’t all that surprised to find the taobao subdomain of this Web site hosting a raft of malware.
Troublesome Trojan Trammels Torrent Sites
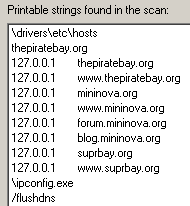 We spotted an interesting behavior from a Trojan dropper that belongs to a family of malware named Ponmocup. The file, update.exe (MD5 89f4ea9f0240239e0d97f202d22af325) leaves behind a payload that, among other things, modifies the Hosts file on infected computers to prevent users from visiting popular Bittorrent sites, including The Pirate Bay.
We spotted an interesting behavior from a Trojan dropper that belongs to a family of malware named Ponmocup. The file, update.exe (MD5 89f4ea9f0240239e0d97f202d22af325) leaves behind a payload that, among other things, modifies the Hosts file on infected computers to prevent users from visiting popular Bittorrent sites, including The Pirate Bay.
It’s an odd behavior for several reasons. We don’t see many Trojans modify the Hosts file anymore because such modifications are so easily reversed. But more to the point: Why would a criminal care whether anyone else be able to browse The Pirate Bay, a Web site known to host torrents of pirated, copyrighted material? And why also block Mininova, which changed its content model more than a year ago and no longer hosts copyrighted files? None of these things make sense.
It seems at first blush like the act of someone who fancies himself a copyright vigilante, sophisticated enough to build a custom tool such as this, but who isn’t smart enough to know which sites to block.
Karagany Isn’t a Doctor, but Plays One on Your PC
![]() A Trojan that pulls a sly performance of now-you-see-me-now-you-don’t disguises itself on an infected system as the Adobe Updater, a real program that’s installed alongside such mainstay applications as the Adobe Reader. This method of hiding in plain sight means the downloader, Trojan-Downloader-Karagany, may remain active on an infected system for an extended period of time, reinfecting PCs even after the more obvious payloads have been cleared up.
A Trojan that pulls a sly performance of now-you-see-me-now-you-don’t disguises itself on an infected system as the Adobe Updater, a real program that’s installed alongside such mainstay applications as the Adobe Reader. This method of hiding in plain sight means the downloader, Trojan-Downloader-Karagany, may remain active on an infected system for an extended period of time, reinfecting PCs even after the more obvious payloads have been cleared up.
During the initial infection, subtlety is this Karagany’s strong suit. When executed, it pulls an act I find slightly more interesting than the conventional file copies itself from one place to another, then deletes the original behavior that is so common among contemporary malware.
In this case, the malware app (which uses an Adobe icon) does copy itself to another location — the Application DataAdobe folder under the currently logged-in user’s account, using the filename AdobeUpdater.exe — but leaves behind a benign program afterward, in exactly the same place as the original, and with the same filename as the original. Watch this video to see just how slick this shell game can be.
[vimeo 17098939]
The Trojan makes a duplicate of a legitimate Windows app (the Microsoft HTML Application Host, or MSHTA.exe), naming the copy with the same filename the Trojan used at the time it was executed, and replaces itself with the renamed MSHTA.exe in precisely the same location. The effect is low-key — the program simply seems to lose its icon.
Rogue AV Spam Invades Multiply, Yahoo Mail
 While nowhere near the size of the mammoth Facebook, the social network Multiply is no slouch. Based in Boca Raton, Florida, the site is designed around not only sharing photos and videos with friends and family, but also a relatively novel concept called social shopping, which permits users of the site to shop together in a virtual marketplace, or even set up an Internet storefront. At last count, according to Multiply’s blog, the site has over 12 million users, which means that the Multiply Market may be one of the largest single shopping Web sites in Southeast Asia, where most of its users live.
While nowhere near the size of the mammoth Facebook, the social network Multiply is no slouch. Based in Boca Raton, Florida, the site is designed around not only sharing photos and videos with friends and family, but also a relatively novel concept called social shopping, which permits users of the site to shop together in a virtual marketplace, or even set up an Internet storefront. At last count, according to Multiply’s blog, the site has over 12 million users, which means that the Multiply Market may be one of the largest single shopping Web sites in Southeast Asia, where most of its users live.
I would never have even known about Multiply (it’s one of nearly 200 active social network sites listed on Wikipedia) if it weren’t for one of our Threat Research analysts, Rhoda Aronce, who hails from the Philippines and uses Multiply to keep in touch with family. She received an odd-looking message that appeared to come from Multiply on her Yahoo mail account yesterday, and it set off alarm bells. Good thing, too, because it looks like a spam campaign targeting Multiply users is trying to infect those users’ computers with a rogue AV that calls itself Antivirus Solution 2010 Next.
The initial spam message uses familiar social engineering tropes: It’s a message that looks like it was sent via Multiply’s servers to Rhoda’s Yahoo mail account. The message body reads
heyy! (username), do we know from some place isn’t it? so here’s a special video i did for you, ull recall me!, pls holler me back!!!, kisses <3
The message is dominated with a photo of what looks like a streaming video window that says Click here to see movie. That’s where the fun begins for researchers, but please, don’t click this at home, especially if you’re in the middle of shopping online. Leave getting infected to the professionals. If you see something like this in your email inbox, just delete the message.
Search Hijacker Adds Files to Firefox Profile
 In September, I posted an item about a dropper which we call Trojan-Dropper-Headshot. This malware delivers everything including the kitchen sink when it infects your system. It has an absolute ton of payloads, any of which on their own constitute a serious problem. All together, they’re a nightmare.
In September, I posted an item about a dropper which we call Trojan-Dropper-Headshot. This malware delivers everything including the kitchen sink when it infects your system. It has an absolute ton of payloads, any of which on their own constitute a serious problem. All together, they’re a nightmare.
Among the payloads, we’ve seen this monstrosity drop downloaders (Trojan-Agent-TDSS and Trojan-Downloader-Ncahp, aka Bubnix), adware (Virtumonde, Street-Ads, and Sky-banners), keyloggers (Zbot and LDpinch), clickfraud Trojans (Trojan-Clicker-Vesloruki and at least three other generic clickers), and a Rogue AV called Antivir Solution Pro. So this is one nasty beast that has no qualms about using the shotgun approach to malware infections.
But we also noticed that it has added yet another intriguing installer to its panoply of pests: It’s a small executable named seupd.exe (search engine updater?) that makes two minor (but obnoxious) modifications to Firefox. The result of these modifications changes the behavior of Firefox’s search bar, the small box that lets you send queries directly to search engines, located to the right of the Address Bar.
![]() The modifications are not immediately apparent unless you try to search Google for something, using either the Search Box or the Address Bar: Instead of sending your search to Google, the browser submits search queries to one of six different domains not owned by Google, but which appear to use the Google API to provide results — and, presumably, earn a little ad revenue on the side.
The modifications are not immediately apparent unless you try to search Google for something, using either the Search Box or the Address Bar: Instead of sending your search to Google, the browser submits search queries to one of six different domains not owned by Google, but which appear to use the Google API to provide results — and, presumably, earn a little ad revenue on the side.
read more…
Malware Threats: What Would Churchill Do?
By Ian Moyse, EMEA Channel Director
 With Christmas fast approaching, (lest we forget the shops have kindly put all the Christmas goods out in September and early October again!) we can expect online attacks to increase as per their normal schedules, ramping up through the end of the year.
With Christmas fast approaching, (lest we forget the shops have kindly put all the Christmas goods out in September and early October again!) we can expect online attacks to increase as per their normal schedules, ramping up through the end of the year.
With apologies to Sir Winston Churchill, never in the field of Internet conflict was so much harm done to so many by so few.
For all the benefits the Internet provides our lives, no single technology has given so few criminals the ability to cheaply and easily target the many. We’ve seen the rise of the dark economy, where far flung cybercriminals trade skills and produce burglary tools for sale, and we live with the consequences every day. Sophisticated attacks target both our computers and our users, through social engineering.
While the increases in cybercrime incidents seem to indicate a greater number of attackers, the reality is that the growth of the Internet itself gives rise to the ever-increasing volume of botnets, keyloggers and spam. The Internet makes us all contactable and, to a degree, easily identifiable. As we surf the Web, we leave traces of our presence in the form of electronic footprints — cookies, blog postings, and of course, our activities on social networks and other online forums.
And yet, no matter what we do to stem the tide, the problems only seem to increase in size and scope.
You can tune in and listen live to more of Ian Moyse’s predictions for next year’s most serious threats in his free Webinar, ThreatNet 2011, Thursday, November 4, at 10am Eastern.



































































