DDoS Attack on Dyn Crippled the Internet
A portion of the internet went down after suffering a crippling blow from a series of global attacks on a cloud-based Internet Performance Management (IPM) company, called Dyn. Major websites including Twitter, Reddit, Spotify and even game servers for Battle Field 1 have been affected.
Malware Using Trump’s Name to Entice Users
With the election swiftly approaching, have you started to see an influx in Donald Trump-themed articles and email spam lately? Beware! Malware authors are in full swing creating threats aimed solely to infect users. They are counting on the polarized emotions to leave users disarmed. Take caution this election season and stay safe online.
School District Has Data Breach via Third-Party Vendor
The value of data is remaining higher than ever, and compulsory schools are finding out the hard way. Recently, a third-party data management vendor used by Katy ISD in Katy, TX, was exposed. The vendor in question, SunGard K-12, considers the incident low risk. Fortunately for the students and their families, the data breach was quickly noticed.
Axis Bank Discovers Unknown Login on Internal Servers
In yet another announcement of a bank becoming a victim of cybercrime, Axis Bank in India has made an official claim to the Royal Bank of India that its servers were compromised. Since the discovery, Axis has launched a full investigation, which has reported no unauthorized monetary transfers or signs of customer data loss.
Android Malware Still Affecting Non-Updated Users
In the past few weeks, the Android Trojan known as Ghost Push has continued to spread across older versions of the Android OS. By rooting itself to a device, the trojan is exceedingly difficult to remove, as even a factory reset will prove unhelpful. By displaying a steady stream of ads, the creators are able to profit from the clicks generated. There is a solution–upgrading your device to either Android 6.0 or 7.0 will stop the malware from propagating, as it is unable to root either of these operating systems.
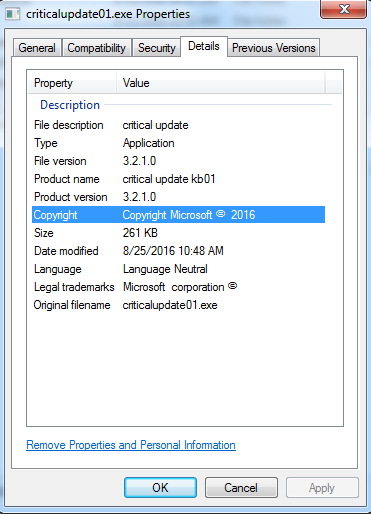
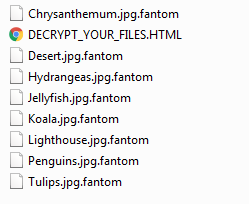
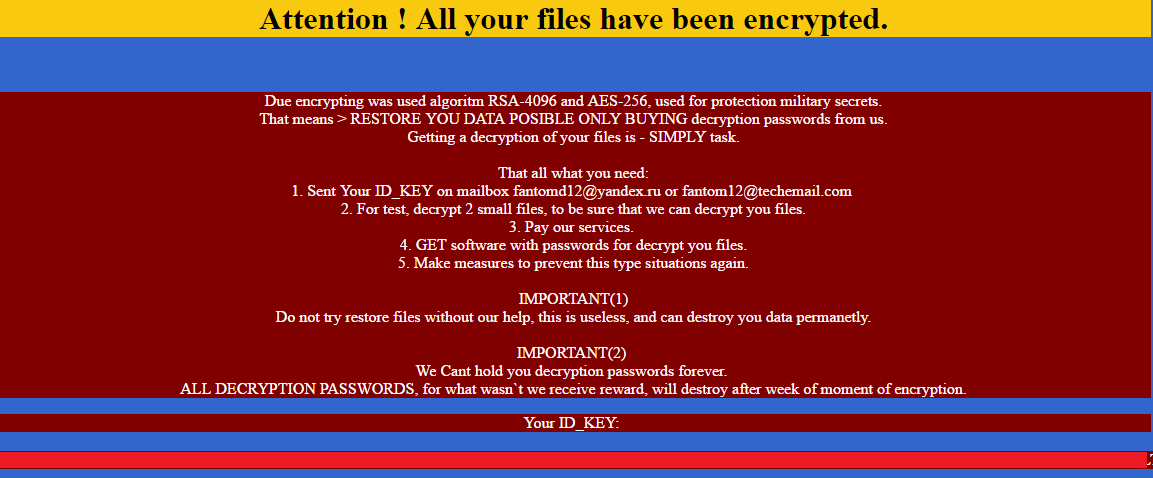
CryPy Ransomware Using Python-Based Encryption
Ransomware authors have taken to new methods of targeting users and improving their profit odds. A a new variant called CryPy ransomware—written using Python—is being used to retrieve multiple RSA key tokens and encrypt a variety of files while allowing some “free” unlocks to the user. I wouldn’t say this is particularly useful, but being able to unlock specific files gives the victim a feeling of hope to recover the remaining and may increase the chances of the ransom being paid.