The ransomware attacks that make headlines and steer conversations among cybersecurity professionals usually involve major ransoms, huge corporations and notorious hacking groups.
Kia Motors, Accenture, Acer, JBS…these companies were some of the largest to be compromised by ransomware in 2021. These were mainly hit with well-known variants, sometimes unleashed by state-backed hacking groups. But it’s key to understand that no “Top 10” list of ransomware incidents paints an accurate – or at least comprehensive – picture of the impact ransomware played over the last year.
That’s because, small businesses and not-for-profit organizations are often hit the hardest by ransomware. Here are a couple factors to consider that might help reframe how we think about ransomware, who’s targeted and why small businesses can’t escape the gaze of ransomware groups.
- Attach Surface vs. Cybersecurity Resources
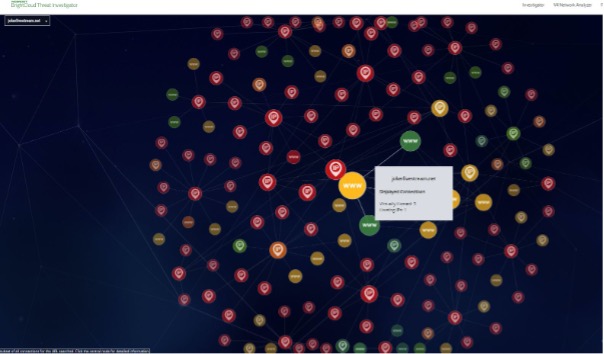
In our 2021 Webroot BrightCloud® Threat Report, we found overall infection rates to be rising fastest in the healthcare, non-profit and arts/entertainment/recreation industries. Schools, local governments and hospitals are some of the most commonly targeted types of institutions, accounting for some 2,400 breaches in 2020, according to the Ransomware Task Force’s (RTF) 2021 report.
We don’t typically think of these organizations as having excess budget earmarked for ransomware actors, so why are they so often targets? What makes them attractive to cybercriminals? It turns out, it’s exactly this lack of resources.
Often operating with limited IT budgets, hospitals, schools and local governments also typically run some of the most complex and difficult to secure networks. Spread out over multiple locations and responsible for hundreds or even thousands of devices – factors referred to as the “attack surface” in information security – make these institutions attractive targets. To make matters worse, a shortage of cybersecurity professionals and budget constraints mean they handle these challenges short-staffed.
As a result, public school systems, police departments and towns were among major compromises in recent years.
- “Average” Ransomware Costs Can Be Misleading
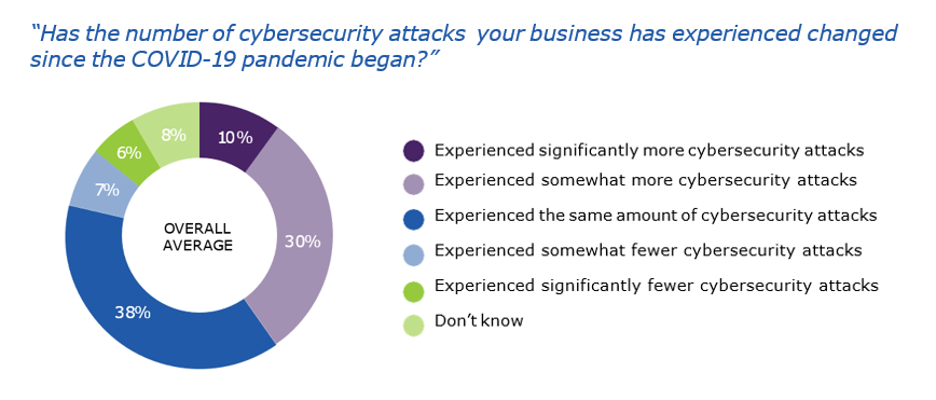
Many security companies justifiably try to quantify the costs of ransomware year over year. While almost all agree both the number of attacks and the demanded ransoms are rising, these stats can obscure the real story.
Leaving aside the fact that they’re almost certainly underreported – businesses tend not to disclose ransomware incidents to avoid negative publicity and fines from regulatory agencies – a few high-profile incidents can drive up averages and distort the perceived cost to small businesses.
“I could never afford a $50 million ransom like the one hackers demanded of Acer,” the thinking goes, “so I must not be worth their time.” While understanding, this conclusion misrepresents the problem.
In fact, the median ransom demand in 2021, according to advanced findings from our upcoming threat report, was $70,000. Still potentially bankruptcy-inducing, this figure is within reach for a far greater number of businesses. Hence, a larger number of businesses are considered acceptable targets by criminals actors.
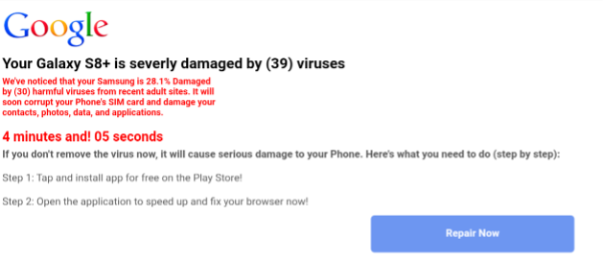
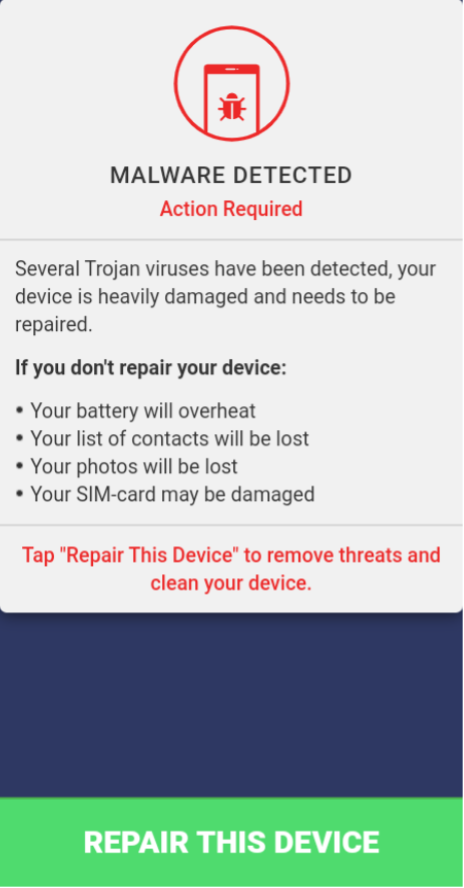
- Ransomware as a Service Changed the Game
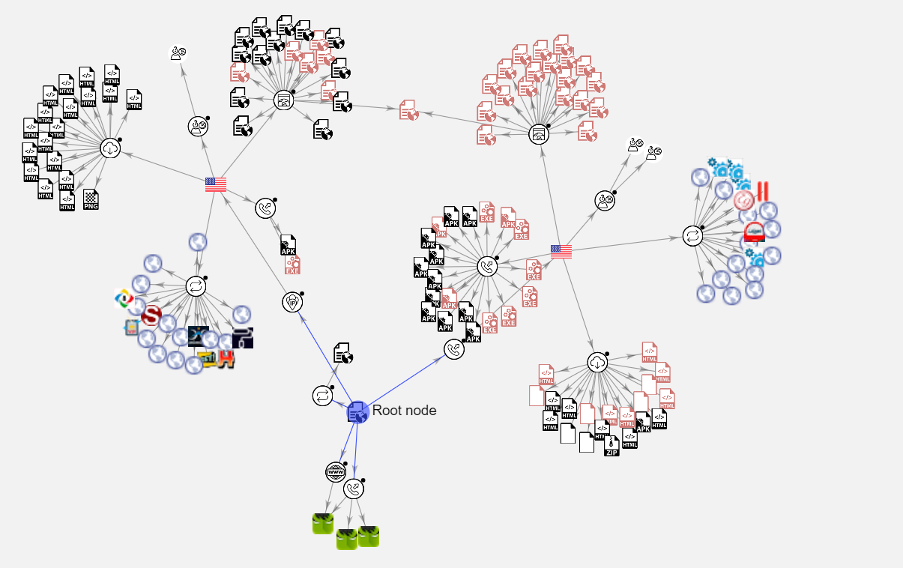
Maybe it was the case once, but malicious actors no longer have to be savvy behind a keyboard. Ransomware as a service (RaaS) is an increasingly popular business model among malicious actors where interested parties can buy ransomware “products” – malicious code meant to encrypt a target’s files – from a developer online.
According to the RTF, “In 2020, two-thirds of the ransomware attacks…were perpetrated by cyber criminals using a RaaS model.”
While supply chain attacks and major breaches of global corporations still require a good deal of technical sophistication, cracking the dentist’s office down the street no longer does. All that’s needed is a working knowledge of the dark web, a connection to a developer with loose morals and some startup capital to purchase the code.
This means casting a wider net with smaller ransomware demands threatens to ensnare more small and midsized businesses than before this business model emerged.
Securing small businesses in the crosshairs
Business owners and the MSPs that secure them can see how a set of factors are converging to increase the cybersecurity risks to businesses of all sizes. Luckily, there are a few steps, relatively easy to implement, that can help these organizations reduce their risk of falling victim to ransomware – or to limit the scope of any successful attacks.
These include:
- Locking down Remote Desktop Protocols (RDP) – As the trends from 2021 emerge, it’s become clear that open RDP ports are the most common method of compromise among small businesses. They’re simply too easy for cybercriminals to discover and exploit, so lock them down.
- Educate end users – The next common method of compromise is phishing attacks, independent of company size. But our research suggests that regular phishing simulations can dramatically reduce click-through rates among frontline users.
- Install reputable cybersecurity software– What used to be the main method of defense against malware is now only a single method of defense, but it’s still a critical one.
- Set up a strong backup and disaster recovery plan– Misconfigurations and user-enabled breaches are almost impossible to stop entirely. Having backups of critical files can reduce the pressure to pay a ransom and undermine the leverage cybercriminals have against a business.
Interested in learning more about ransomware and its effects on businesses? Download our eBook on the Hidden Cost of Ransomware.