The global pandemic that began to send us packing from our offices in March of last year upended our established way of working overnight. We’re still feeling the effects. Many office workers have yet to return to the office in the volumes they worked in pre-pandemic. For MSPs, that makes up a good portion of their clientele.
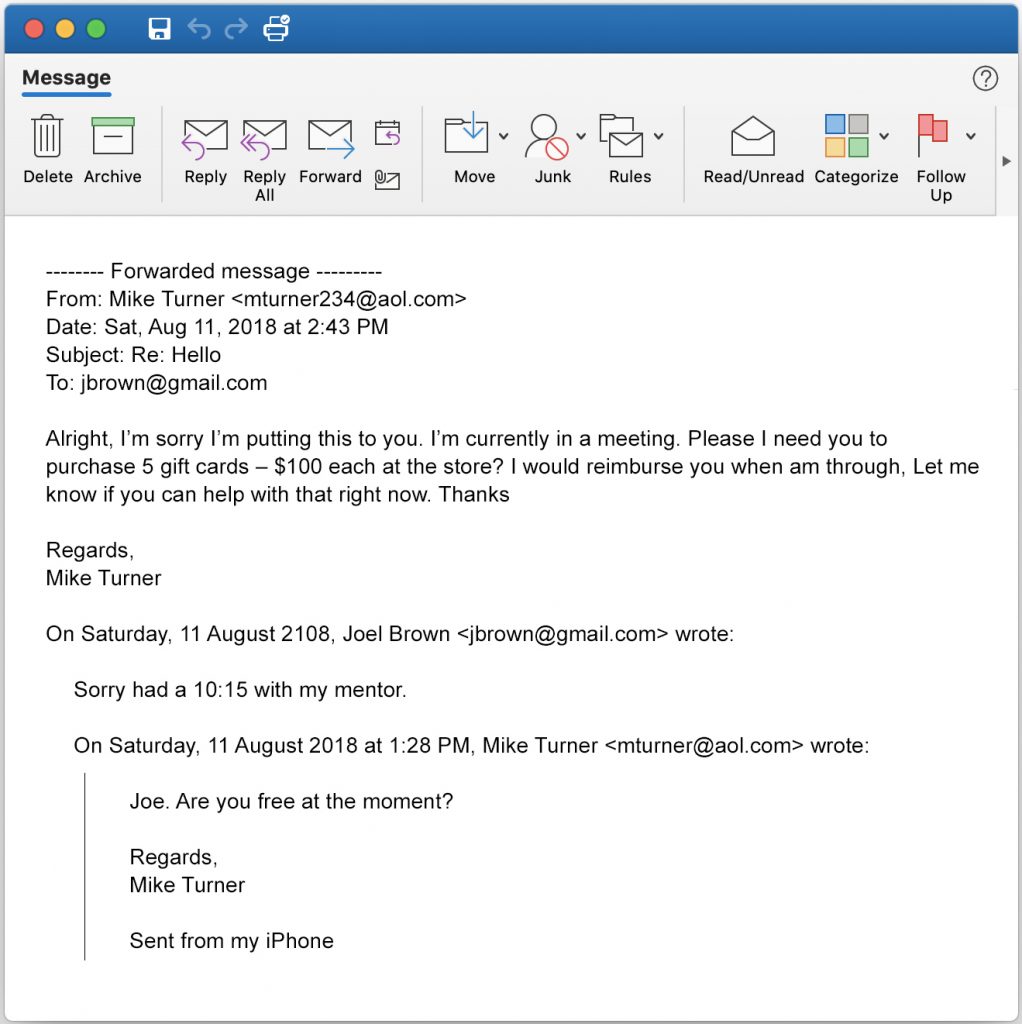
Remote workers were abruptly pulled out from behind the corporate firewall, immediately becoming more susceptible to the targeted attacks of cybercriminals. Acceptable use policies could no longer be easily enforced, home devices became work devices, and employees distracted by life around them became more likely to click carelessly.
What’s worse, because the pandemic was affecting more or less all of us at the same time, cybercriminals had a virtually limitless pool of targets on which to test out new scams. Phishing scams imitating eBay skyrocketed during the first months of product shortages brought on by COVID-19. Scam emails claiming to be from Netflix rose by more than 600% in 2020.
We were fish in cybercriminals’ collective barrel. Now, even with vaccinations rising in the U.S., many companies are rethinking the way they work. It’s up to MSPs to have a strategy for security remote workers, because they’ll likely need to serve more than ever before.
Find out how to ensure your clients’ remote workers are resilient against attacks across networks in this informative conversation between ChannelE2E and MSSP Alert editor Joe Panettieri and his guest Jonathan Barnett. In addition to being a network security expert and senior product manager for Webroot’s DNS solution, Barnett brings 20 years of experience as the head of his own MSP business to the podcast.