As a security professional it’s hard to say ‘I told you so’ but as far back as 2009-2010 Webroot was saying that the endpoint market was broken and that a new approach to stopping malware infections on endpoints was needed. At that time the rest of the endpoint security market was particularly quiet on their efficacy at stopping attacks they just kept pointing at meaningless and some would say gamed ‘independent’ test results about how great their efficacy was.
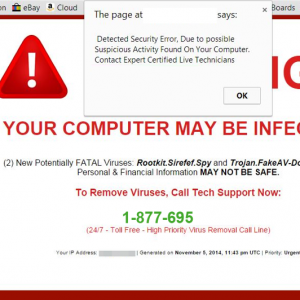
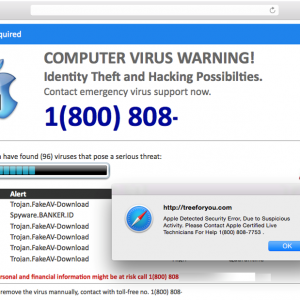
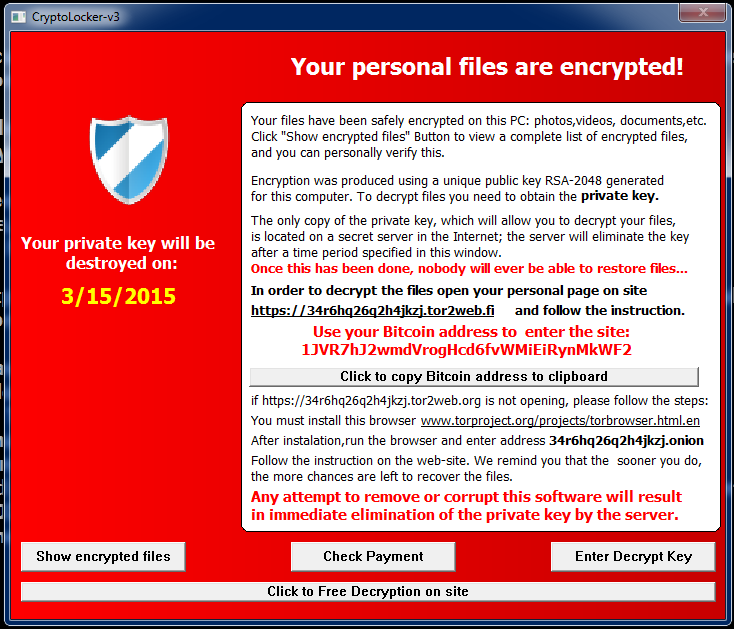
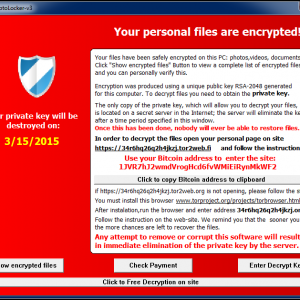
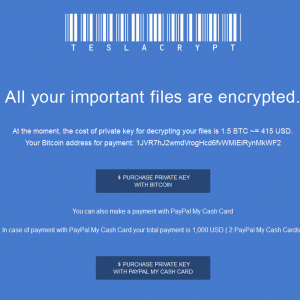
Of course the ‘chickens came home to roost’ and that efficacy was thrown under a Mack Truck over the past couple of years by the volume and frequency of new malware and its variants that was hitting endpoints. The attack patterns changed too. No longer did you have broad-based attacks now you had targeted, individualized and especially in 2014 continuous attacks aimed at known individuals in organizations.
The availability and open nature of today’s communications plus the exploitation by the big Internet players and other actors has meant everyone’s life can be pried into and used to make life more convenient, but with that convenience comes a dark side (that for many observers is seemingly winning and cannot be thwarted.) Frankly neither I, nor Webroot believe that.
Attackers’ methods can be turned against them and the attentions of the priers thwarted by only allowing them to access what you want them to access. Lots of security vendors believe that too. If those who want manipulate get smart then we need to get smarter. We can have smarter cybersecurity and we can make it consciously work together to make life very difficult indeed.
At Black Hat Webroot will be demonstrating and talking about some of the security solutions and collective threat intelligence that by working together make endpoints, servers, networks and the Internet safer for us all and are turning previous failures into success. In the end its choosing battles and winning the wars that will matter.












 Released: Webroot’s 2015 Threat Brief
Released: Webroot’s 2015 Threat Brief