If you’ve ever been infected with serious malware, you may have assumed the culprit is a person sitting in the basement of their mom’s house, or a small group of people huddled in a garage somewhere. It’s really not that simple. There’s a whole global cyber underground network that’s working diligently to make all this happen for you. It’s the lucrative cyber black market. Mostly everyone has heard the term “black market” at least a few times. It’s referenced in many movies and is often heard on the news when speaking of criminal activity and the purchasing of illegal materials or services.
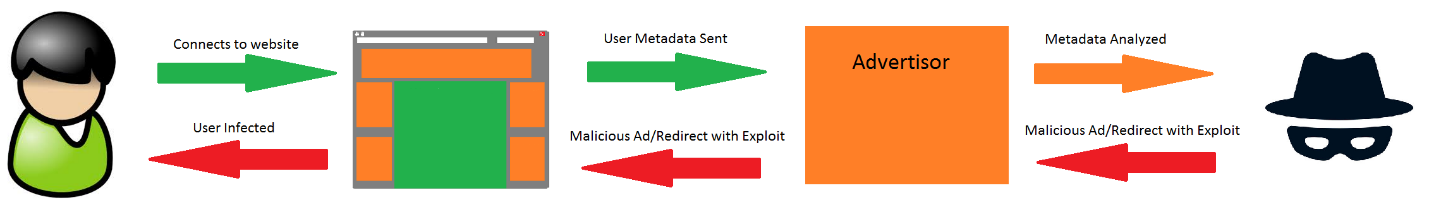
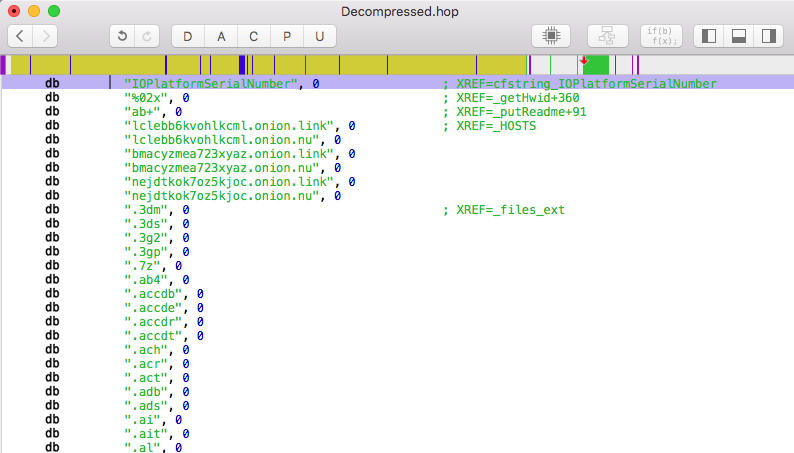
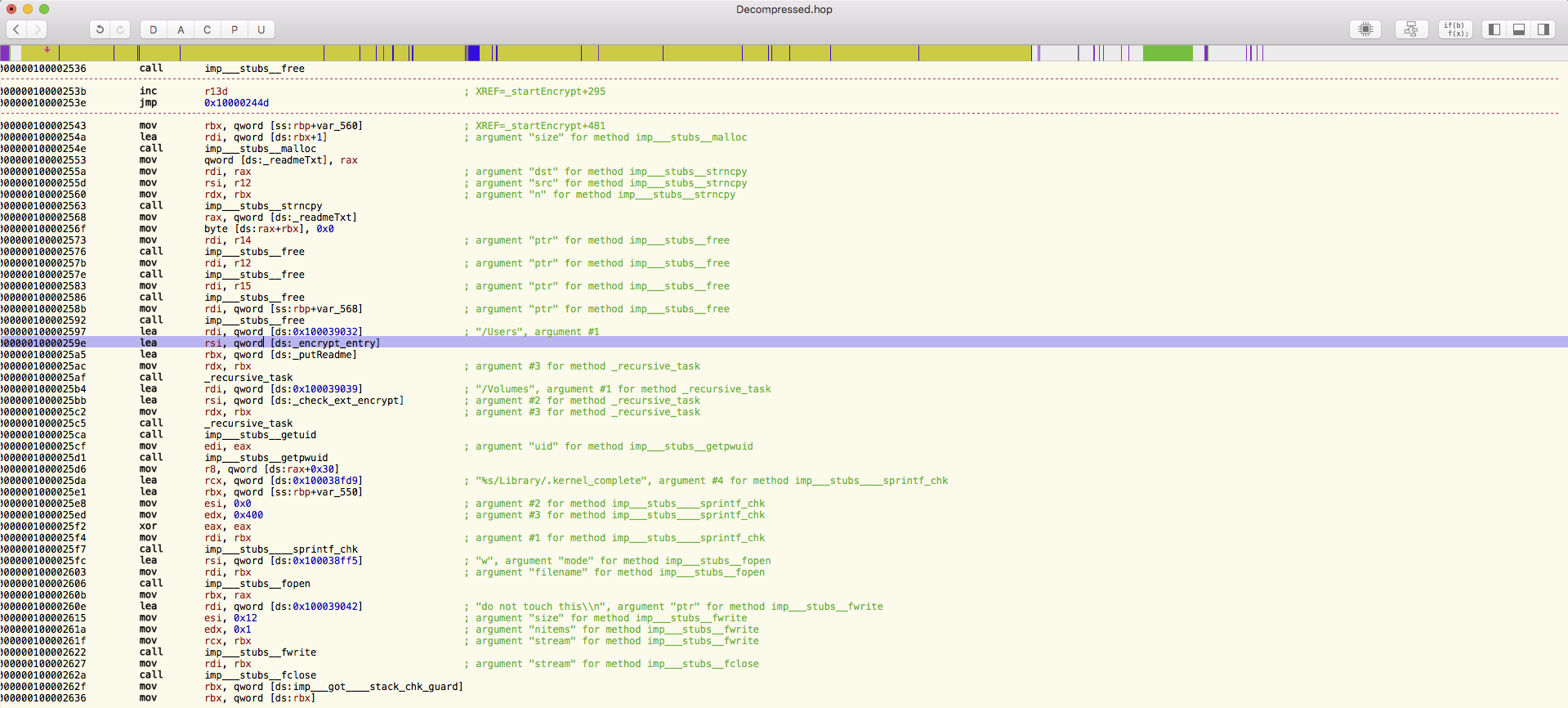
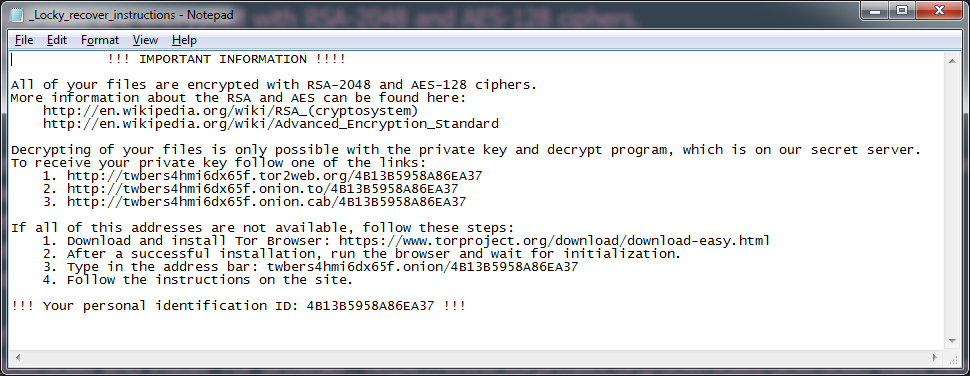
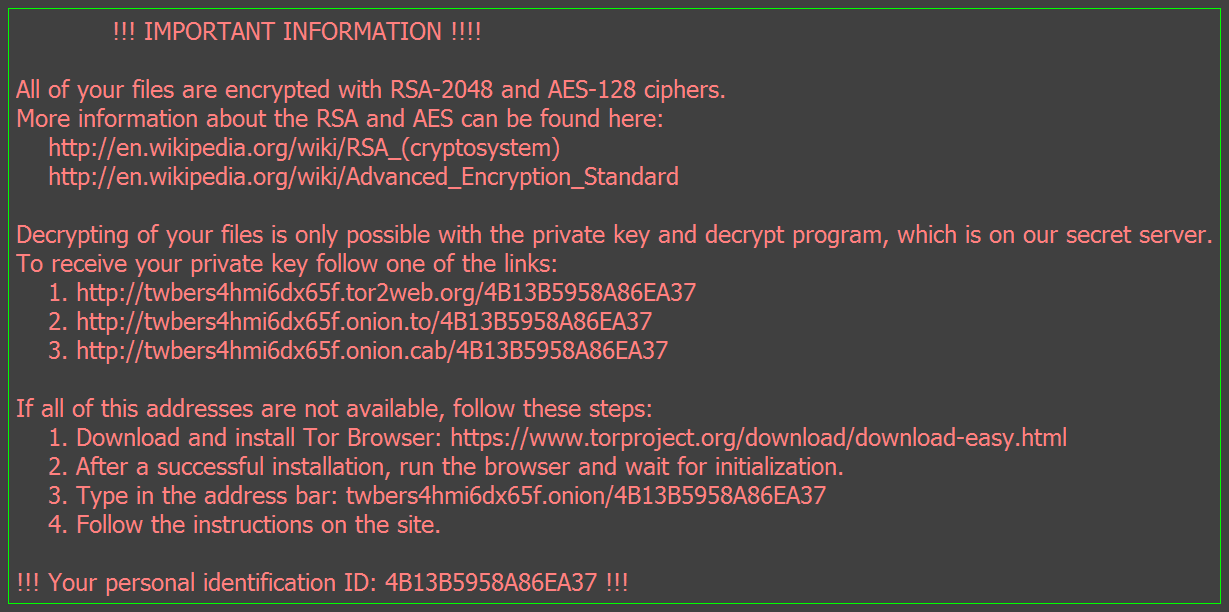
Malware-as-a-Service is a prosperous business run on the black market that offers an array of services and isn’t just limited to malware or bits of code. And you don’t have to be a computer expert either. Anyone can purchase code that will cause harm to a person’s computers or even hold it for ransom. But once purchased, what are you going to do with it? How will investing in this piece of malware return a profit? There’s still the challenge of getting it out there, getting your potential victims to run the payload for the newly purchased malware on their computer. And most importantly, cashing out on the investment. This is where the entire business model of Malware-as-a-Service comes into play.
It’s all offered in the cyber black market and functions no different than the global markets we hear of. Due to its low key nature, it’s difficult to say exactly how much money is generated from Malware-as-a-Service in this market. But it would be no surprise if it stretched up into the billions. In this market it’s possible to purchase all the necessary pieces to make it as easy as possible for the investors to profit.
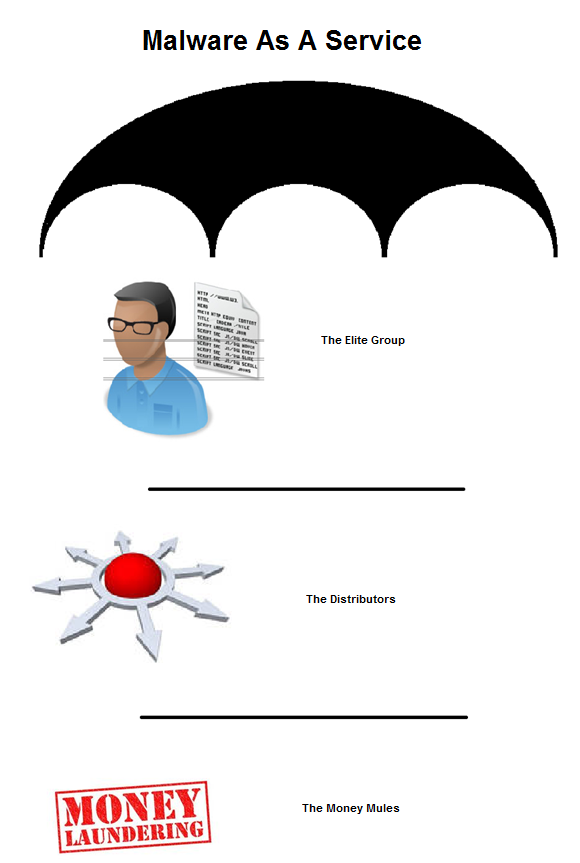
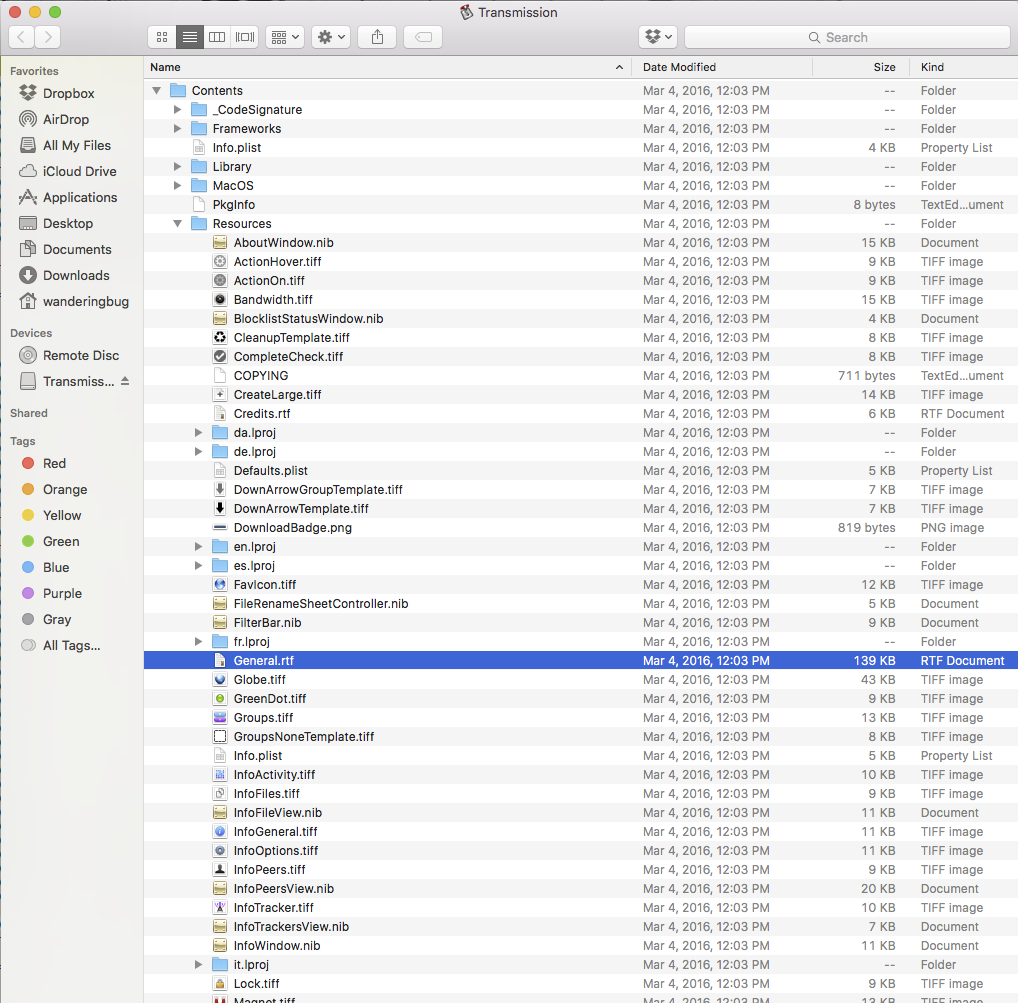
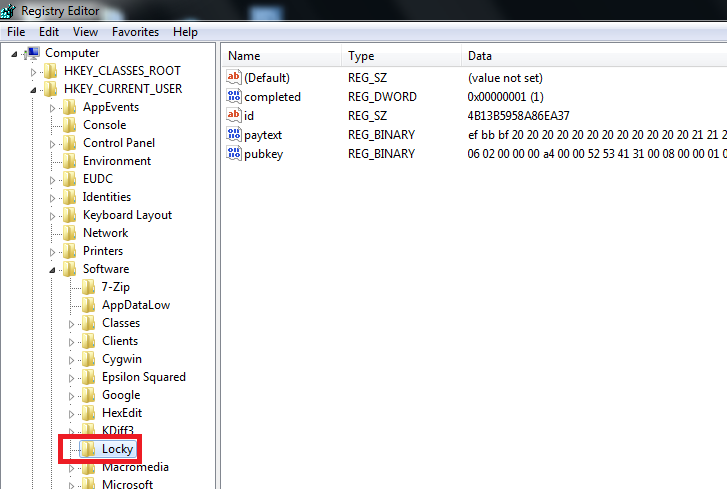
First level: The highly skilled elite programmers or engineers who write malware, develop exploits, and are general researchers. This can be an individual or individuals working together.
Second level: Here are the spammers, botnet owners, distributors, hosted system providers. These people are also skilled, but not always elite. This is where the distribution is handled
Third level: The money mules, treasurers, financial data providers.
These three levels fall under the umbrella of Malware-as-a-Service that can be sold and purchased as an entire package or individual services by a vendor.
The individuals involved aren’t always strictly black hat. There are also grey hat hackers, otherwise known as freelancers who are simply looking to make a profit. A programmer can sell a zero day exploit to the vendor of a software as a bounty. However that same exploit might be able to fetch a far greater profit if sold on the black market. A perfect example of this is Facebook, who offers a minimum of $500 for anyone who can hack their site. With over 700 million users, a Facebook exploit can sell for a pretty hefty price in the black market. As malware becomes more profitable this type of business model will continue to grow.