by Connor Madsen | Mar 25, 2016 | Threat Lab
A lot happens in the security world and many stories get lost in the mix. In an effort to keep our readers informed and updated, we present the Webroot Threat Recap, highlighting 5 major security news stories of the week.
Microsoft Addresses Macro Malware Issue
With macros being a major vulnerability point in Microsoft Office software, the 2016 version of the product line will now offer protection against these infections. By allowing network admins to block execution of any macro that attempts to download content from the Internet, this will greatly reduce the number of systems that are compromised.
http://news.softpedia.com/news/microsoft-adds-new-feature-in-office-2016-that-can-block-macro-malware-502058.shtml
Ransomware Takes Aim At Healthcare
In the past week, three U.S. hospitals were targeted by ransomware attacks that left them in varying levels of functionality. Fortunately for patients, all hospitals have returned to full capacity, with little to no patient information being leaked. It is still unclear if the hospitals paid the ransom, however the cases are under FBI investigation.
http://www.bbc.com/news/technology-35880610
NASA Email Servers Hit with DDoS Attack
Recently, a group of hackers linked to Anonymous has made claims that they used a DDoS attack to take down NASA’s email servers all around the world. However, that claim appears to be unsubstantiated, as NASA’s main website was still accessible during the apparent outage. The attack was perpetrated because the hacker group claims that NASA is keeping important information regarding ISIS withheld from the public.
https://www.hackread.com/hackers-ddos-shutdown-nasa-website-email-server/
Local Utilities Need to Increase their Security Measures
In a recent study done by the Verizon RISK lab, it was determined that while many local utility services believe they are quite secure against an information-stealing attack, they are actually a major offender of vulnerabilities. The study also revealed that one customer, Kemuri Water Company, had a decade-old system infrastructure while also using a SCADA platform with direct internet access and no two-factor authentication.
http://www.zdnet.com/article/the-future-of-our-city-services-cyberattackers-target-core-water-systems/
Majority of IT Pros Use Basic AV Security Solutions
It was revealed recently that the vast majority of IT professionals believe that using only a basic Antivirus software is enough to defend against the latest cyber attacks. The study also showed that only 15% applied additional defensive measures. Fortunately for consumers, the trend is moving towards ever-improving security protocols and finding better ways to catch the latest malware variants.
http://www.computing.co.uk/ctg/news/2452094/ninety-seven-per-cent-of-it-professionals-think-standard-antivirus-software-will-stop-zero-day-attacks

by Connor Madsen | Mar 18, 2016 | Threat Lab
A lot happens in the security world and many stories get lost in the mix. In an effort to keep our readers informed and updated, we present the Webroot Threat Recap, highlighting 5 major security news stories of the week.
Credit Card Fraud Now Quicker Than Ever
There are thousands of cases of credit card fraud that occur every year, usually through a merchant breach. Lately, however, a new process has emerged and has shown to take almost no time at all, while also being nearly foolproof. By quickly attaching a face-plate skimmer to a credit card processor, hackers can retrieve any customer data they collect later by simply removing the skimmer or remotely connecting to the device via bluetooth.
http://www.csoonline.com/article/3043662/security/credit-card-terminal-goes-from-safe-to-compromised-in-less-than-three-seconds.html#tk.rss_news
Bank Breach in Bangladesh
It recently came to light that hackers had breached Bangladesh’s central bank and attempted to withdraw $101 million USD from their US-held account. The U.S. Federal Reserve allowed the initial transactions to occur, but the overall attack was halted when Deutsche Bank employees noticed a spelling error for the recipient party. While some of the cash had already been transferred to offshore casinos, the remainder that had been withdrawn was returned.
http://www.bankingtech.com/455732/typo-spells-confusion-in-101m-cyber-bank-heist/
Anti-DDoS Firm Hit with DDoS Attack
It has been confirmed that in the past week, the cyber security firm Staminus, has been the latest target of a severe DDoS attack. The attack left the Staminus website down for several days and finally resulted in a large information dump, containing mainly customer information. The information dump was preceeded by a note from the hacker that listed off various “tips” for running a security company, a likely jab at the security flaws used to initiate the breach.
https://nakedsecurity.sophos.com/2016/03/15/attacker-leaves-security-tips-after-invading-anti-ddos-firm-staminus/?utm_source=Naked+Security+-+Sophos+List&utm_campaign=7230822a23-naked%252Bsecurity&utm_medium=email&utm_term=0_31623bb782-7230822a23-454898153
Major News Sites Target of Malvertising
Recently, several high-profile domains were infiltrated by cybercriminals with the intent to distribute ransomware via the Angler Exploit Kit. With ransomware being a simple method for attackers to affect a large audience (as well as bring in a nice profit), more companies should be taking a closer look at their own systems and patching any vulnerabilities. While the attack lasted less than 24 hours, thousands of daily visitors to high-traffic sites such as the New York Times, BBC, and Newsweek could be affected.
http://www.csoonline.com/article/3044588/security/malvertising-campaign-hits-new-york-times-bbc-others.html#tk.rss_news
Typosquatting, Latest Mac OS X Scam
Cybercriminals are always on the lookout for the next method of targeting end-users. This time, they’re focusing on poor spelling. By implementing a method called ‘typosquatting’, attackers have been registering common US company domains using the “.om” suffix (belonging to the country of Oman), in hopes that people misspelling “.com” will be redirected to one of their phony sites. Aimed mainly at Mac OS users, when they land on a fake site, users are directed to a fake Adobe Flash update that actually attempts to install Genieo, a common Mac adware variant.
https://threatpost.com/typosquatters-target-apple-mac-users-with-new-om-domain-scam/116768/

by Blog Staff | Mar 17, 2016 | Webroot Blog
If you’re one of the people who is still stubbornly holding onto Windows XP (which stopped receiving support and security updates as of April 8, 2014), it’s time to let go. Likewise, if you’re using an outdated version of your preferred internet browser, it’s time to update. Right now. Why? In both scenarios, you’re putting your personal online security at risk any time you browse the internet. Without current web browser support and critical security updates from Microsoft, your PC may become vulnerable to any number of harmful viruses, spyware, and other malicious software which can steal or damage your identity, personal finances, and information.
Microsoft Pulls the Plug on Windows XP; Users Should Upgrade
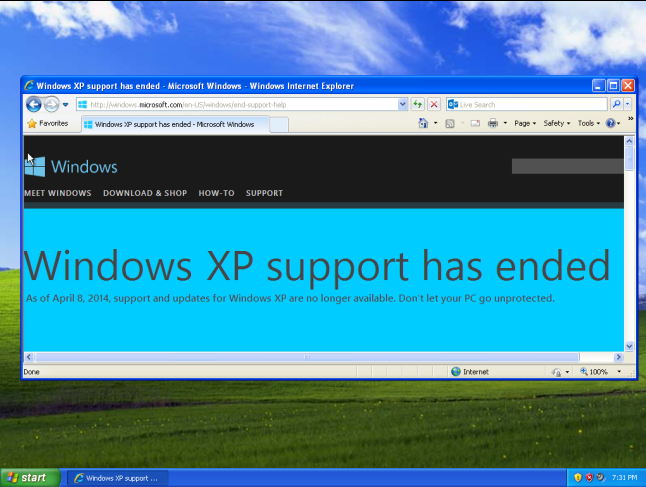
(Source: howtogeek)
Nearly two years ago, Microsoft finally made the decision to stop supporting the widely popular OS (operating system) after a 12 year run. Windows XP faithful (and there were many) were encouraged to say their farewells to the beloved OS and move on to newer Microsoft technologies, or continue to use XP at their own risk as the OS was no longer receiving security updates. Unfortunately, many users chose the latter option, leaving their computers susceptible to a myriad of threats. Worse yet, people stubbornly continue to use Microsoft XP, despite the security risks. If you fall into this category, I strongly advise you to upgrade to a version of Windows that Microsoft still supports.
For more information on the end of XP support as well as how to upgrade, you can check out this Microsoft FAQ.
Using an Up-to-Date Internet Browser on a Supported OS is Important As Well
Making sure your operating system is supported is critical, but it’s not the only step users need to take to stay secure. If you’re using a supported OS, but fail to keep your internet browsers updated, you leave yourself vulnerable every time you browse the web. Likewise, if you’re using an updated browser on an OS that’s no longer supported, same thing. Thus, browser support is also crucial for a safe internet-using experience. Here’s the current support status of each major web browser:
Internet Explorer:

(Source: Microsoft)
Beginning January 12, 2016, only the most current version of Internet Explorer available for a supported operating system will receive technical support and security updates. Internet Explorer 11 is the last version of Internet Explorer, and will continue to receive security updates, compatibility fixes, and technical support on Windows 7, Windows 8.1, and Windows 10. In other words, if you’re using any prior version of I.E., you’re at risk and it’s time to update.
Fortunately, Internet Explorer 11 offers improved security, increased performance, better backward compatibility, and support for the web standards that power today’s websites and services, so the transition should prove a comfortable one. Microsoft encourages customers to upgrade and stay up-to-date on the latest browser for a faster, more secure browsing experience. You can download the latest version of Internet Explorer here.
Google Chrome:

(Source: Google Images)
Chrome, Google’s wildly-popular take on the internet browser, came onto the browser scene (and subsequently onto users computers) in 2008. Now, it’s estimated that Chrome is the most widely-used browser on desktops, at 58% worldwide usage share.
Unlike Internet Explorer, Chrome automatically updates each time it detects that there’s a newer version available, so users don’t have to worry about being on a potentially-outdated version of the browser. However, last November, Google announced it will end support for Chrome on some older operating systems by April 2016, which means that less than a month from today, Chrome will stop getting updates if your computer is running any of the following operating systems:
Windows Vista, Windows XP, OS X 10.6 Snow Leopard, OS X 10.7 Lion and OS X 10.8 Mountain Lion
The April 2016 deadline is actually an extension to the life cycle of Google Chrome on Windows XP. Google originally announced back in October 2013 that support for Chrome on XP would end by April 2015, before pushing that deadline back to December 2015. For more information on system requirements as well as download links for different operating systems, check out this Google support page.
Mozilla Firefox:

(Source: Mozilla)
Mozilla’s Firefox, created back in 2002, still remains a popular browser choice for users. Largely thanks to the decline in Internet Explorer usage, Firefox reportedly took over the number two slot for desktop browsers in February 2016.
Like Chrome, Firefox is set by default to automatically update to the latest version. You can find a list of all Firefox releases here.
As far as operating systems go, here are the ones currently supported by Mozilla: Windows XP SP2, Windows Server 2003 SP1, Windows Vista, Windows 7-10, Mac OS X 10.6-10.11. You can learn more about getting the latest version of Firefox on an older version of Windows here (although you should really not be using Windows XP at this point, as outlined earlier).
Safari

(Source: Apple)
Sure, some Mac users prefer to use Chrome or Firefox. However, Safari (the default internet browser on Mac OS X that was originally released in 2003) is also used by many Mac users worldwide.
While the browser doesn’t update automatically, users can easily check for updates by opening the App Store and clicking on ‘Updates’ in the toolbar. If there’s a new version of Safari available, users just need to click the ‘Update’ button (and enter their Apple ID), and the latest version will be installed.
To keep Safari up-to-date, Apple encourages users to upgrade to the latest version of OS X. Safari 9, which is currently in version 9.0.3, comes bundled with the latest version of OS X, El Capitan. However, users who are still using OS X Mavericks can also update to the latest version of Safari. You can find out more information on this Apple support page.
With so many options, updates and upgrades available today, it’s easy to find yourself using an outdated operating system or a internet browser that is no longer supported, and putting yourself at a security risk as a result. Hopefully this blog post and the included hyperlinks will help you take the necessary steps in ensuring your operating system and browsers are up-to-date, which in turn, will help safeguard your identity and personal information. As always, it is also important to have an up-to-date antivirus program installed to protect your computer, in addition to an up-to-date browser and OS.

by Nathan Wyman | Mar 14, 2016 | Threat Lab
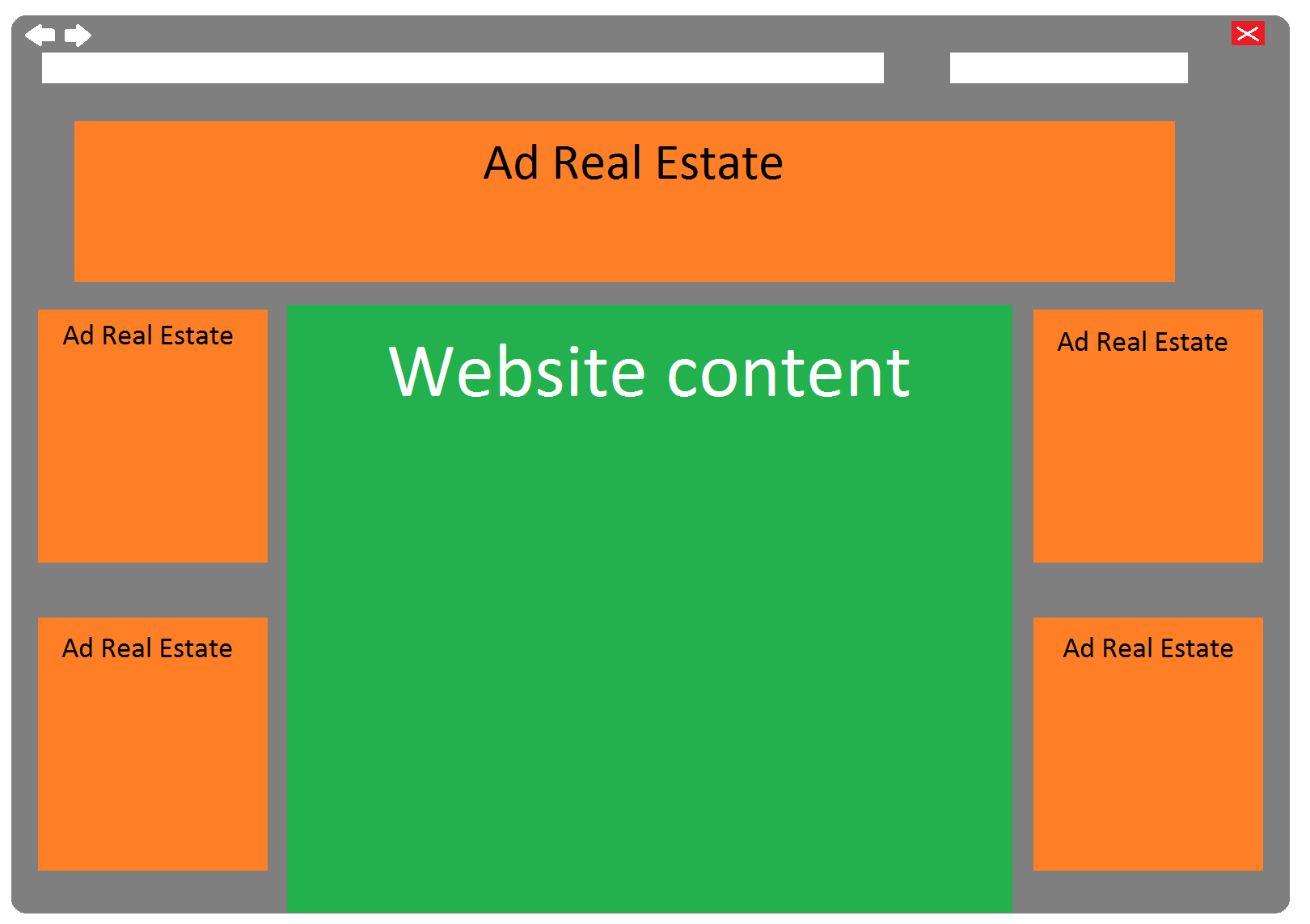
Advertisements on the internet are no longer just a nuisance. They are now also potentially dangerous. Even sticking to widely used and trusted websites can be risky, as the banner ads they contain may be carrying malicious code.
“Malvertising”, a combination of “malware” and “advertising”, is the technique of using trusted ad networks to deliver malware-loaded advertisements to users on trusted websites. This is not a new technique, but over the last couple of years its use has grown exponentially by cybercriminals because it is so effective.
According to David Kennerley, Sr. Threat Research Manager at Webroot: “Malvertising is a big problem and its return on investment for fraudsters suggests it’s not going away anytime soon.”
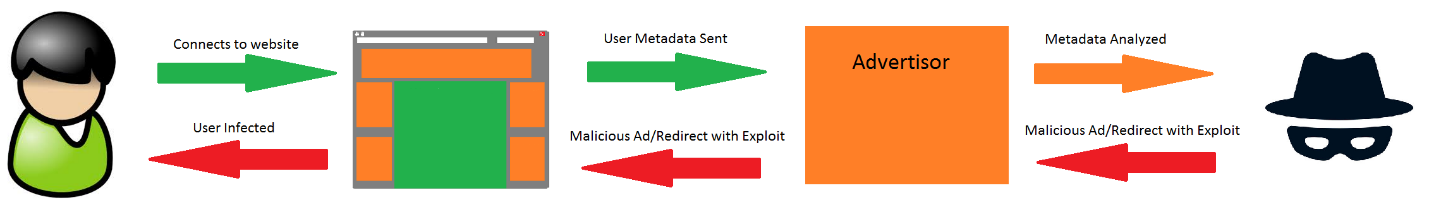
Most websites that have advertisements use “ad networks” to manage those ads, giving the site options for what type of ads to deliver to visitors. In a malvertising scenario, a cybercriminal will either hack into an ad network’s server or even sign a fraudulent contract with an ad network, posing as an advertiser in order to gain trust. They will then upload a seemingly legitimate advertisement that is loaded with malicious content, such as a Flash or Javascript exploit. The ad network unwittingly adds this malicious ad into its database so that its customers can choose it as one of multiple rotating ads. Or, it can take more of a social engineering approach and appear on your screen based on your browsing habits, which are tracked by tracking cookies.
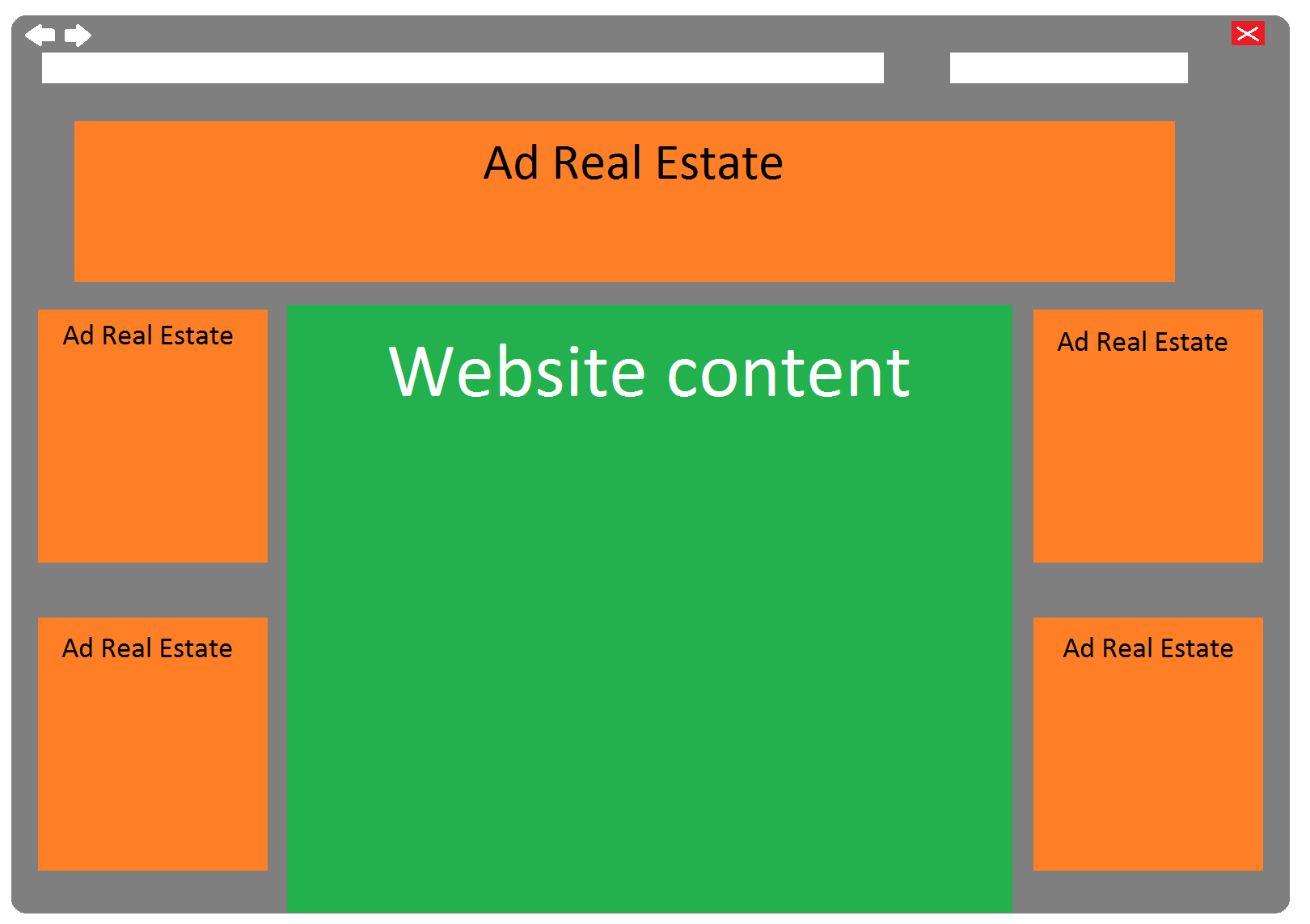
“Unfortunately, simply keeping to trusted websites no longer means you’ll stay safe,” said Kennerley. “The outsourced, distributed and chaotic nature of the online advertising industry means that even the world’s most popular websites have no visibility on the ad content displayed on their pages or its original source.”
In recent months, an additional level of complexity has been employed in these types of attacks: “Fingerprinting”, a method of uniquely identifying computers based on meta-data and file dumps. As online advertisers move away from human transactions and toward real-time ad bidding, cybercriminals are finding ways to better target their victims. Ad networks provide user meta-data to advertisers so that they can better advertise to consumers, but this same data can be used by cybercriminals to identify systems that can be exploited. For instance, if the meta-data reveals that a PC’s Adobe Flash is not up to date and a known exploit exists for their version of Flash, they will identify that PC as a target for attack.
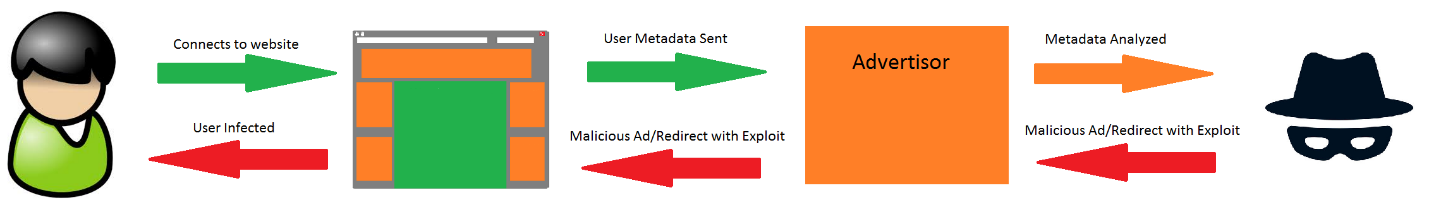
In addition to identifying potential victims, cybercriminals also use fingerprinting to identify networks and devices to avoid. For instance, if they choose to target only people in specific countries and avoid people in their own country, they can do so using geolocation data. This technique has also been used to evade security researchers by avoiding networks of security companies, making it more difficult to replicate and research these types of attacks.
With malvertising gaining popularity among cybercriminals, protecting yourself from this type of attack is critically important. “Internet users should keep their browsers fully patched, with appropriate in-built phishing and malware protection switched on,” advised Kennerley. “Browser add-ons should be kept up-to-date, with auto-play turned off; or better yet, disable or remove these commonly exploited add-ons completely. Ad-blocking software is becoming a must and of course a strong endpoint protection product is essential.”

by Connor Madsen | Mar 11, 2016 | Threat Lab
A lot happens in the security world, and many stories get lost in the mix. In an effort to keep our readers informed and updated, we present the Webroot Threat Recap, highlighting 5 major security news stories of the week.
Tax Season Leads to Rise in Phishing Attacks
As we’ve seen in the past, corporations preparing their taxes for the April deadline are a lucrative target for phishing attacks. Most recently, Seagate Technologies had such a breach in which all current and former employees’ W-2 information was compromised. This incident follows a trend of attacks that target employees by spoofing the CEO’s email address and asking for highly sensitive information.
http://www.csoonline.com/article/3040626/security/three-more-firms-hit-by-targeted-phishing-attacks-seeking-w2-data.html#tk.rss_news
Ransomware Targets Mac OS X
In the past week, it was brought to light that a new form of ransomware had hit the market and was aimed specifically at Mac users. KeRanger comes bundled with the Transmission Bittorrent client and remains dormant for three days to avoid quick detection or suspicion of the torrenting app itself. After that time period, it gathers sensitive information about the Mac and uploads to a Command & Control server, thus starting the process of encryption.
https://www.webroot.com/blog/2016/03/07/18611/
Android Users Hit with Banking Malware
Recently, a new form of banking malware, labeled as Spy.Agent.SI, has been targeting Android mobile banking users. The program will lock the device until the user enters their bank login information from one of the targeted bank apps. Currently, it appears to be focused on several large banks in Australia and New Zealand, and only impacts users who downloaded the fake Adobe Flash Player app from a third-party app store.
http://www.csmonitor.com/World/Passcode/2016/0307/Sophisticated-banking-malware-targets-Android-users?mc_cid=db5948860e&mc_eid=aa7c64b687
Facebook Password Reset Vulnerability Found
A vulnerability was discovered this past week in Facebook’s password reset functionality. While a brute-force attack would be impossible on the facebook.com main website, due to a lock-out feature that triggers after a certain number of failed password tries, several of their other domains do not have this capability. This lack of security in the less trafficked sites within the facebook.com domain allowed the researcher to perform a brute-force attack on his own account, and successfully gain access to the account.
https://nakedsecurity.sophos.com/2016/03/08/how-one-man-could-have-broken-into-any-facebook-account/?
Hotel Chain Major Target for PoS Malware Attack
This week, Rosen Hotels & Resorts Inc. announced that they had fallen victim to a PoS malware infection on their credit card processing systems, which had first been discovered over a year earlier. The company is still unsure how many customers or locations were affected by the attack, which focused primarily on cardholder information, but have begun notifying customers whose information may be compromised.
http://news.softpedia.com/news/rosen-hotel-chain-had-a-pos-malware-infection-for-17-months-501530.shtml?

by Blog Staff | Mar 10, 2016 | Webroot Blog
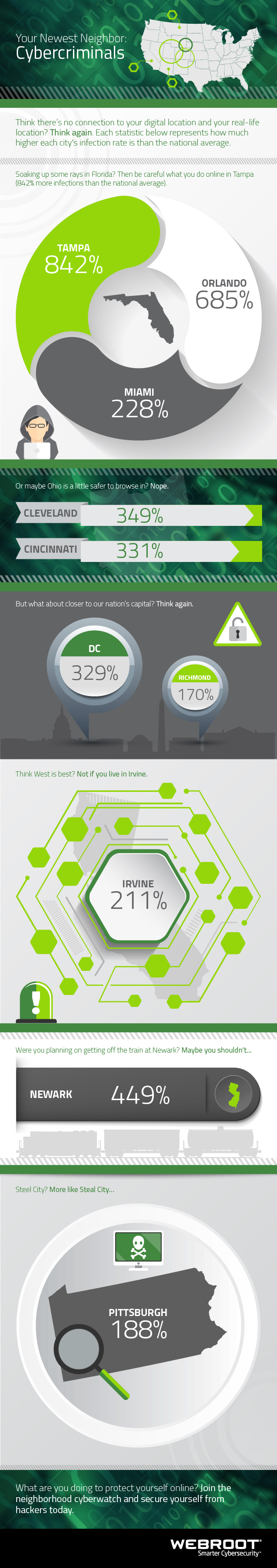
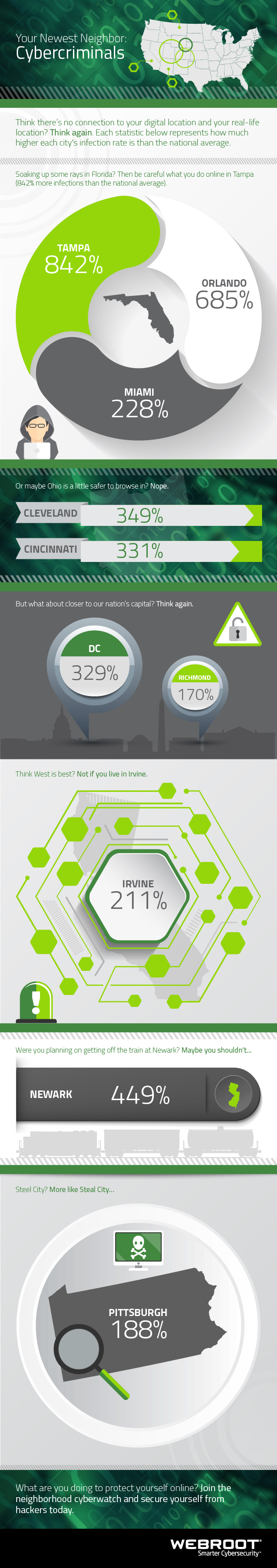
Myth: There is no link between your real-life location and your digital one.
The truth is that the two are very much connected. Perhaps more importantly, then, is what this means when it comes to your personal security. If the state or city in which you live is a hotbed for cybercriminal activity, your chances of being infected online increase significantly. Couple this with the fact that hackers are constantly refining their attack methods and finding new ways to make a profit, and you have yourself a potential recipe for personal information loss disaster.
Fortunately, you can prevent that from happening and stop those cybercrooks right in their tracks. How? By making sure your devices are protected. With cybersecurity that actually works. It also helps knowing which states and cities hackers choose as their favorite targets. The infographic below breaks it down.
by David Kennerley | Mar 7, 2016 | Threat Lab
Seemingly every day, we’re reminded that companies need to work harder to stay secure during a time where cybercrime is rampant and many organizations remain vulnerable to attack. I’ve recently been speaking to the press about what can and should be done to mitigate these risks. I hope the following questions and answers will help shed some light on some key problems many organizations face, and help you decide what’s best for your business.
What happens if an organization focuses too much on the technology aspect of security and not enough on people and process?
Unfortunately, an organization is only as strong as its weakest link – and in terms of security, employees are by far the weakest link.
Technology plays an essential role in any defense, but at the same time technologies cannot stop an employee giving their details out over the phone to someone they believe is from the IT department. And it cannot stop an employee using their corporate password for on their favorite social media sites or writing down their hard to remember passwords.
Relying purely on technology as an organization’s only form of defense is extremely short-sighted; failure is inevitable.
How often are companies attacked because of a vulnerability caused by employees or company processes?
It’s hard to put an exact number this. But from experience, I would suggest it’s a very high percentage. Why wouldn’t it be? Cybercriminals spend so much time, effort and money defeating a technology or defense when employees are such an easy target.
In terms of hackers getting in, the most common issues are misuse of social networking, weak passwords and password re-use, privilege creeping, malware and lack of system patching. But the real danger is employees being unaware of internal security policies or the ones that unfortunately do not care enough and are careless and complacent.
How can CIOs and CISOs go about strengthening their strategy around people and process to ensure cyberattacks aren’t successful?
There’s no magic wand. There’s an infinite number of initiatives that can be introduced to help mitigate risk, all at differing costs and complexity. In simple terms, it’s about completing comprehensive risk assessments, creating policies and understanding industry best practices, evaluating possible technologies, and then, implementing a solution. More than anything, the plan needs buy-in at all levels and needs an appropriate budget.
Training should always be at the heart of an organization’s security program as technology alone will not stand up against a motivated attacker. Everyone within the organization should be made responsible for the security of its assets.
It’s also vital that personnel understand the technologies they are asked to manage and monitor. The intelligence gathered by security systems needs to be understood, so when an attack occurs, it is detected at the first possible opportunity with the correct processes and procedures, then followed.
How can CIOs and CISOs approach internal training and education in regard to security?
Employee involvement is crucial for the success of an organization’s security strategy. Creating a security task force whose members rotate so each employee has eventually been part of the task force is a great way to get everyone involved. Each task force could have a ‘security champion’, who would be the person who identifies the most beneficial improvement to current security processes. This system encourages employees to think actively as well as creatively about security to improve the company’s security.
There is often a disconnect between what employees know they should do security-wise, versus what they actually do in practice. This is one of the most challenging parts of cybersecurity training and education. In these cases, businesses need to make sure it is clearly explained what is prohibited and why – using real world examples of the repercussions of not following procedure. What might seem harmless to an employee, like using an unsecure WiFi network, could cause a business serious problems further down the line.
There’s no point just preaching security, it should be made fun. It’s also important to understand if the information given has been taken in. This is where regular security tests play a vital role. Bad security practices should not be tolerated if appropriate training and guidance has been given. At the same time good security practices should be rewarded.
Can you provide an example of an organization that suffered a major cyberattack because their people and process strategy was not up to scratch?
The breach at Target Corp in late 2013 springs to mind for a number of reasons. It is understood the attack initiated at a third party vendor, an air conditioning subcontractor through a phishing email. User education with regards to the opening of emails may have been able to stop such an attack from escalating.
An assessment by security experts at Verizon noted that while Target had a password policy, it was not followed. A file containing valid network credentials was found stored on several servers, with weak or default passwords used on many internal systems.
It was also reported that many systems were found to be unpatched, something a patch management policy should have covered even after Target’s security systems warned of possible issues. No credible incident response plan was in place, as a Target statement at the time highlighted that after the company learned criminals had entered the network, the team decided it did not warrant immediate follow-up.
Do you expect to see people and process strategies around security improving this year?
Security is finally climbing up organizations’ agendas, so hopefully improvements around people and processes will continue to be made.
Communications and information flow between the organization and its employees is vital – the risks and potential consequences need to be understood by employees through continued user education. It’s arguably the most cost effective approach to improving the security posture of any organization.
However, cybercriminals only need to find one hole in the defense, whereas as security professionals, we have to secure all. It’s never going to be an easy task, but sound user education and relevant processes are now more important than ever and should never be underestimated.

by Blog Staff | Mar 7, 2016 | Threat Lab
Palo Alto Networks recently discovered ransomware hidden inside of the torrenting app ‘Transmission’. While this may come as a shock to those that still believe the Mac is a fortress that can’t be broken, the rest of us are not shocked at all. In fact, a few months back I wrote a blog warning Mac users not to dismiss Mac malware. It is time to take Mac security seriously. Apple does a great job for the most part, but in order to secure your information and your devices, you need a good Antivirus product.
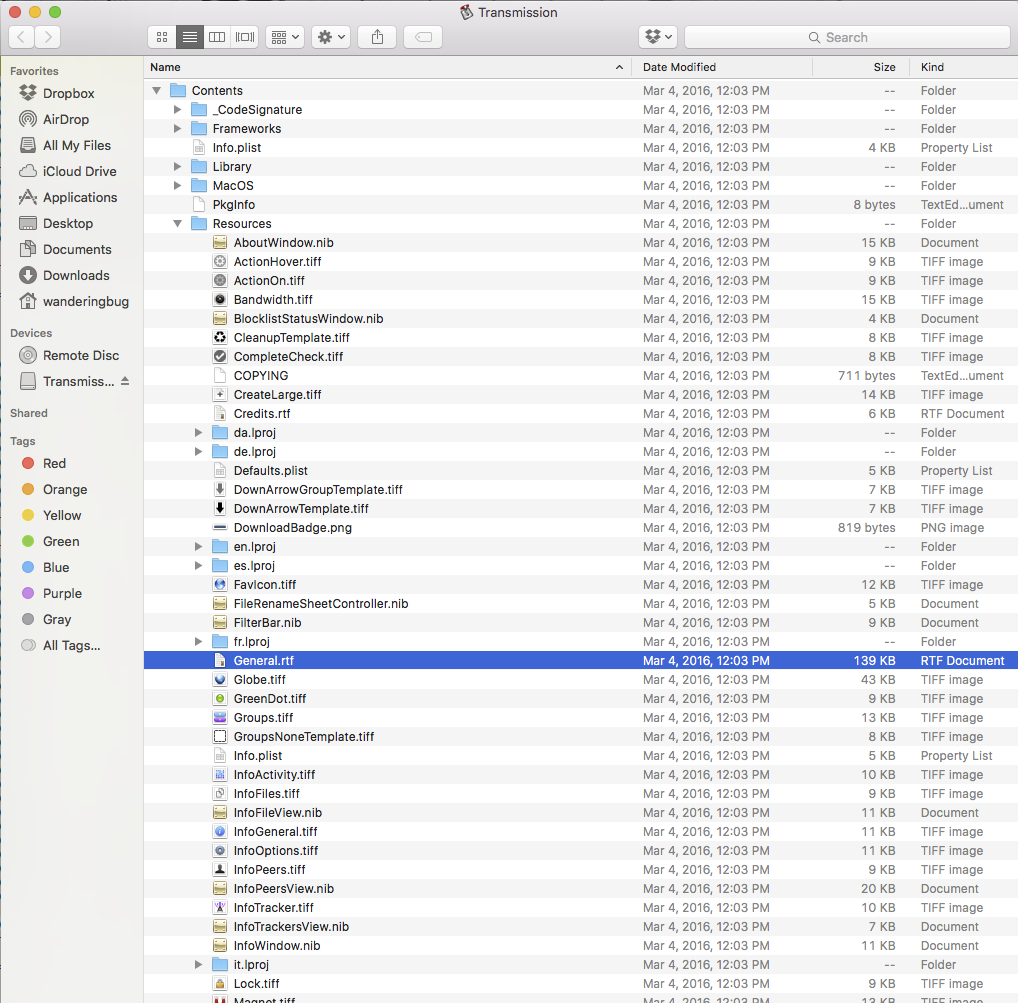
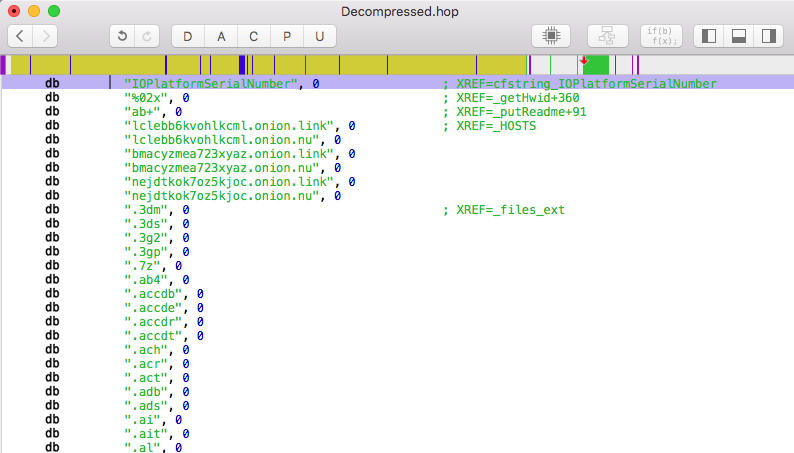
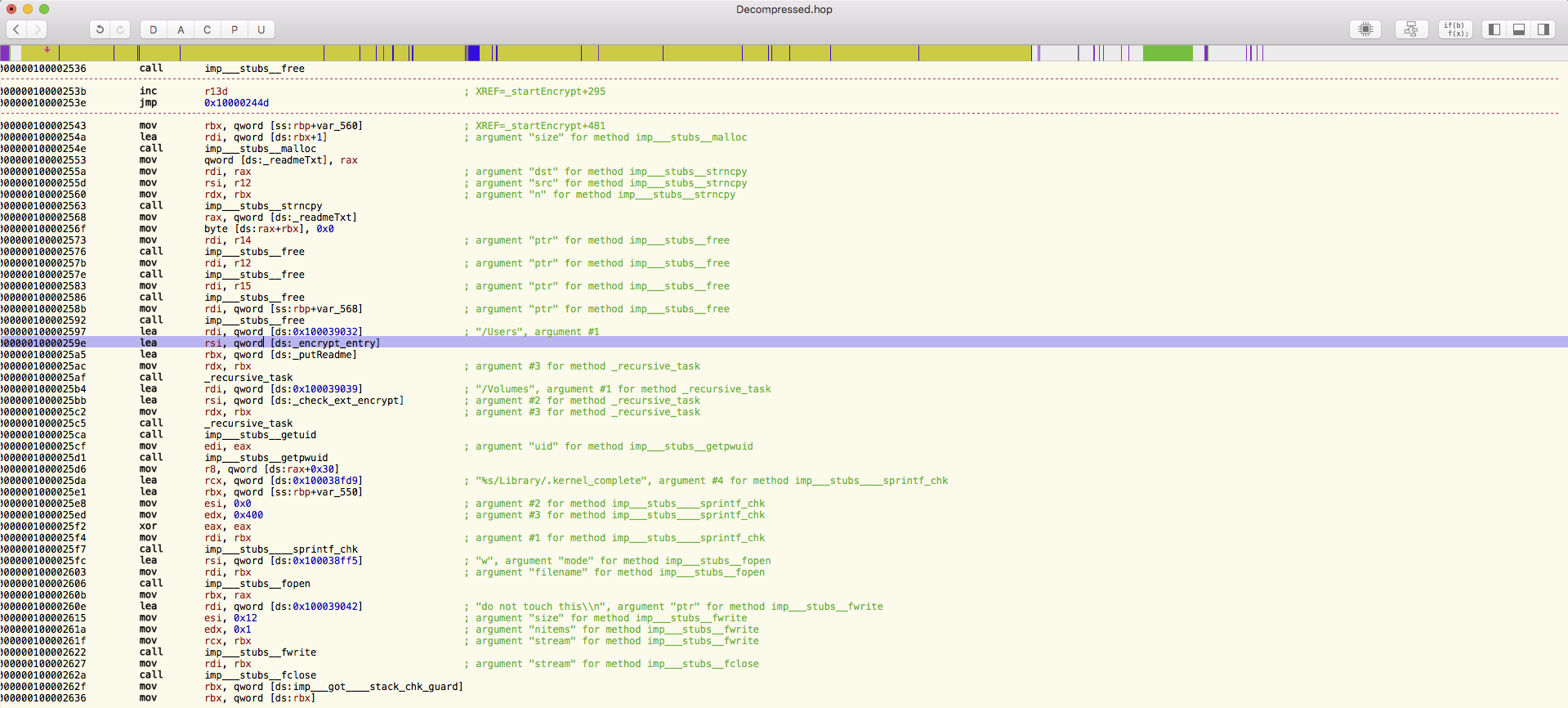
Back to the threat at hand. This ransomware is bundled in with the Transmission Bittorrent client as a file called “General.rtf”. For most, this file looks like a simple real text file. However, it is actually a Mach-O 64-bit executable file that will execute three days after you run Transmission. This helps keep the ransomware hidden so that users wouldn’t suspect the app they are using for torrenting, but rather the torrents that they are pulling down as the source of infection.
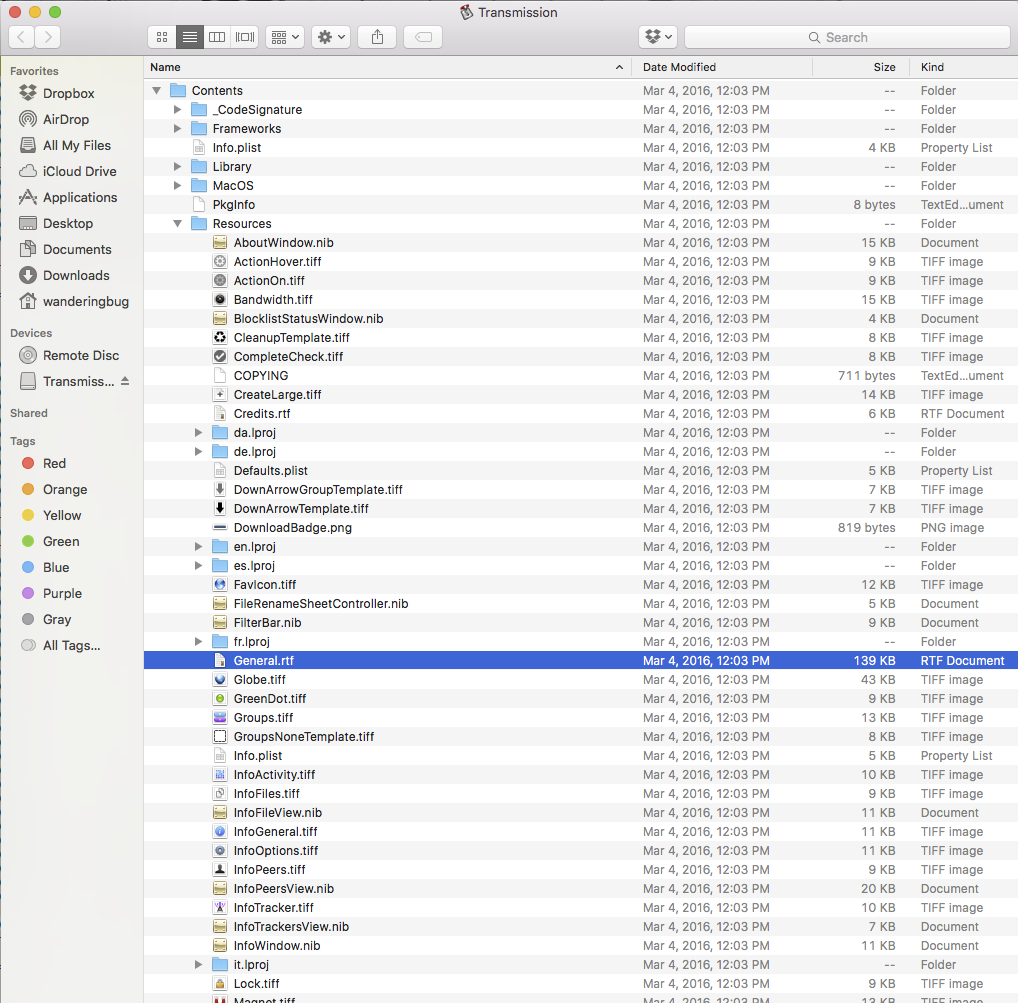
After the three days, the app executes and drops a file called “kernel_service” into the user’s library directory. This process is named in such a way so as to confuse anyone that looks in Activity Monitor into believing that it is a system process. It then drops three more files in the user’s library: “.kernel_pid”, “.kernel_time” and “.kernel_complete”. It will collect the infected Mac’s model name and UUID then upload the information to one of its Command and Control servers.
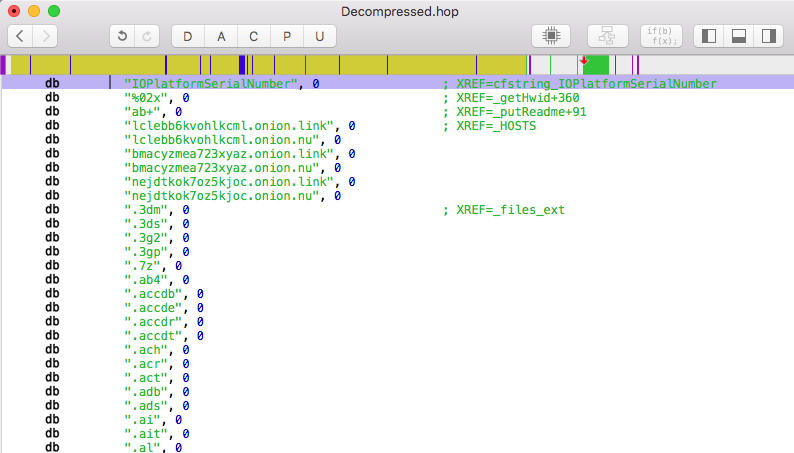
These servers will respond with a file named “README_FOR_DECRYPT.txt”, in which it explains how to get the key for decryption and the price for the key in bitcoins. The ransomware is able encrypt around 300 different types of file extensions that it finds in the “/Users/” directory and changes the file extension to end in “.encrypted”. This means that the family pictures that you keep on your Mac will now be labeled “GrandCanyon2010.jpg.encrypted” and cannot be opened.
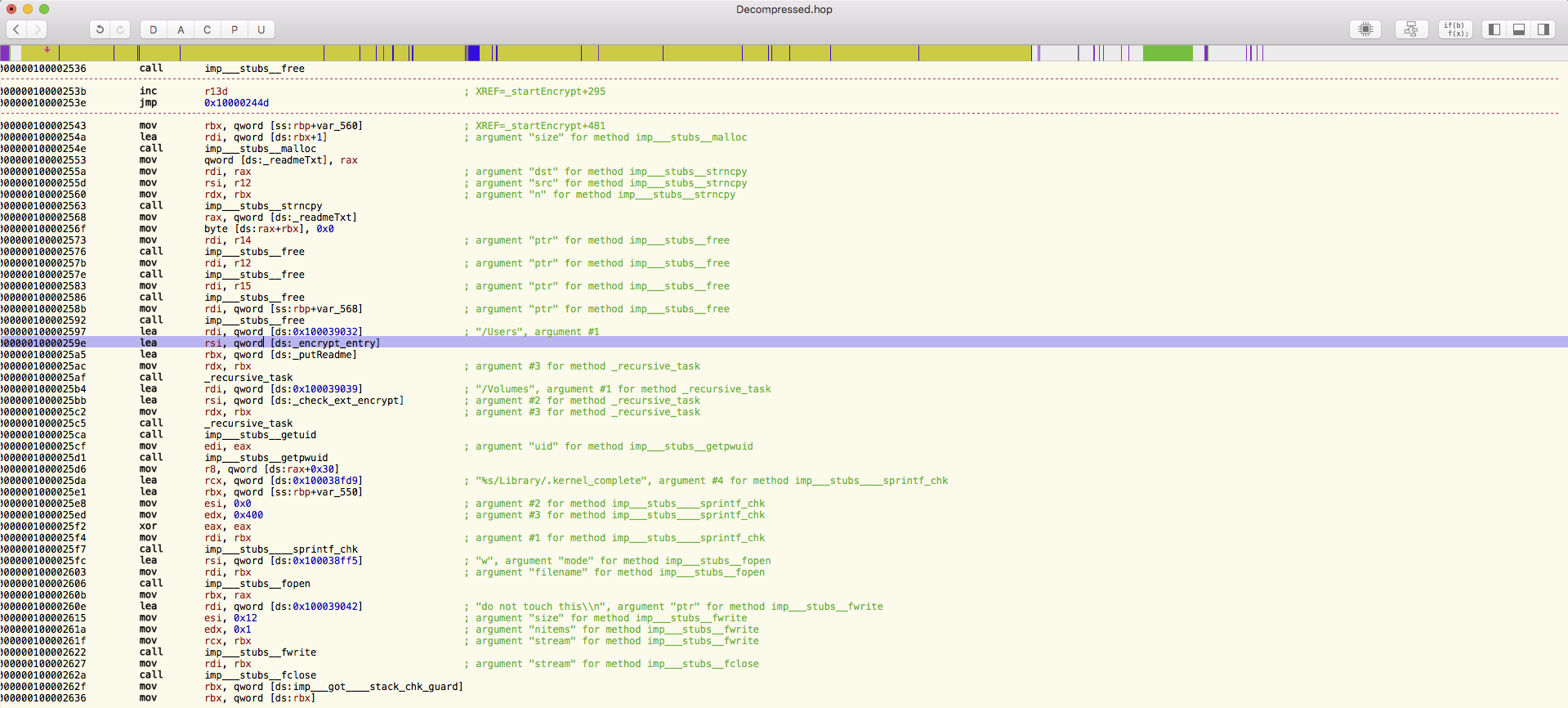
One of the most important things to note is that the program is still a work in progress. There are many functions that have been found in the code that are not currently being used, like the ability to encrypt your Time Machine backup as well. This of course is the second wall of defense for many people, who believe that because they have a Time Machine backup, they can always just roll back their Mac if something happens.
To add some more context into the expansion of ransomware into the Mac OS, our David Kennerley recently commented in Global Security Mag:
“Given the potential gains for attackers, it’s no surprise that they are now diversifying and targeting OS X – a popular system with a large target base. Add to this the fact that many people believe they are safe from such malware when running OS X, this ransomware has the potential to impact a huge number of people.”
You can locate the full article here.
I’ve said it before and I will say it again: Mac malware is real. Don’t be an Apple user that finds this out the hard way.

by Mike Malloy | Mar 4, 2016 | Threat Lab
On Monday of this week, Webroot joined Cloudera, the leading provider of modern data management and analytics systems built on Apache Hadoop, in announcing Open Network Insight (ONI) Project, a database and tools designed specifically for cyber security incident response. ONI will enable security analysts and responders to manipulate the massive amounts of data generated within an enterprise to isolate and investigate both internal and external threats. And because we have years of endpoint-to-cloud experience here at Webroot, we will participate in the project by helping to design the data models for endpoint data.
ONI matches our own Webroot vision of security being an information problem. If you can apply the right data at the right time to decide if you’re being attacked or infiltrated, you can defend yourself. Our SecureAnywhere products put this vision into action by applying massive threat intelligence in the cloud to defeat potential threats on our customers’ desktops and smartphones. ONI will enable an organization to bring together all the relevant data about their network, their users, and their devices in one massive, but easily manipulated database, so they can find and defeat attacks.
Hadoop has been growing rapidly in popularity within the cyber security community, being used in building very large-scale databases of security intelligence data such as network logs, event data, and other data types needed by security analysts. Hadoop combines power, speed, and flexibility, which are the hallmarks of a good data platform. Cloudera has extended the open source base with Cloudera Enterprise, a portfolio of tools to create, manage and analyze large scale databases.
The initial prototype of ONI was created by data scientists at Intel. They created a database which is updated with more than 20 billion network events per day within the Intel corporate network. Then, using proprietary and open source visualization tools, they created a security workbench which allows them to identify and investigate potential threats.
Webroot is excited to be part of Open Network Insight, and excited to be working with Cloudera and Intel to bring this vision to reality. We will update the Blog with our progress.

by Connor Madsen | Mar 4, 2016 | Threat Lab
German Hospitals Latest Ransomware Target
In the past week, several German hospitals have reported ransomware attacks on their internal systems. While one of the hospitals was able to minimize the damage by isolating the infected server, Lukas Hospital wasn’t as fortunate, as their system had been encrypted before they could react properly. Fortunately, the hospitals in question were able to restore the lost data using backups that are performed regularly.
https://www.helpnetsecurity.com/2016/02/26/crypto-ransomware-hits-german-hospitals/
China Accused of Hacking Norwegian Companies
Recently, the head of Norwegian Intelligence came out to publicly accuse China/Chinese hackers of accessing highly valuable military information. This accusation is based upon the methodology typically used by Chinese hackers and the evidence showing geolocation of IP addresses, the language used in the coding, and the types of malware that were used. Currently, it is thought that the vulnerability was a targeted spear-phishing attack on several companies, though no official source has confirmed it.
http://www.scmagazine.com/norway-officially-accuses-china-of-stealing-military-secrets/article/479574/
DROWN Attacks Leave HTTPS Servers Defenseless
Researchers have recently discovered a new method for man-in-the-middle attacks between clients and an SSLv2 server, which is no longer up-to-date, but also still widely used. Unfortunately for end users, there is little that can be done if the system admins haven’t ensured the vulnerability is resolved, though discontinuing use of SSLv2 would eliminate this type of threat completely.
https://www.helpnetsecurity.com/2016/03/01/drown-attack-breaks-tls-encryption-one-third-of-all-https-servers-vulnerable/
Software Updates, The Backdoor To Your System
Every computer runs system or software updates, often without the express consent of the user, but this could have unexpected results. With the proper access to push the update and a way to make it appear authentic, an attacker could send malicious content while seeming to pose no threat to the system. While nearly every operating system has this type of failure point, more and more developers are working towards ensuring updates are only done when they are properly signed.
http://arstechnica.com/security/2016/02/most-software-already-has-a-golden-key-backdoor-its-called-auto-update/
Wendy’s Breach Affecting Financial Insitutions
It was recently found that several Wendy’s locations had been targeted by a point-of-sale malware attack, used to steal customer credit card information. The breach has been larger in scale than previous attacks, and it appears the money being drained from the accounts is in significantly higher amounts. It is currently unknown how many locations have been affected, but it’s likely to be the stores that are using the older card-swipe method over the improved chip-card reader.
http://krebsonsecurity.com/2016/03/credit-unions-feeling-pinch-in-wendys-breach/