Staying a Step Ahead of the Hack
Hackers, never at a loss for creative deception, have engineered new tactics for exploiting the weakest links in the cybersecurity chain: ourselves! Social engineering and business email compromise (BEC) are two related cyberattack vectors that rely on human error to bypass the technology defenses businesses deploy to deter malware.
Social Engineering
Social Engineering is when hackers impersonate trusted associates or acquaintances to manipulate people into giving up their passwords, banking information, date of birth or anything else that could be used for identity theft. As it turns out, it’s easier to hack our trust than our computers. Social engineering covers a range of tactics:
- Email from a friend or family member – A hacker gets access to the email password of someone you know. From there, they can send you a malicious link in an email that you’re more likely to click on because it came from someone you trust.
- Compelling story (pretexting) – This includes urgently asking for help. This can read like, “Your friend is in danger and they need your help immediately – please send me money right away so they can get treatment!”
- Standard phishing tactics – Phishing techniques include website spoofing emails appearing to come from an official source asking you to reset your password or confirm personal data. After clicking the link and entering the info, your security is compromised.
- “You’re a winner” notifications – Whether a lottery prize or a free trip to Cancun, this tactic catches many off guard. It’s known as “greed phishing” and it takes advantage our fondness for pleasure or weakness for the word “free.”
Business Email Compromise
Business email compromise is a targeted attack against corporate personnel, usually someone with the authority to request or fulfill a financial transaction. Victims execute seemingly routine wire transfers to criminals impersonating legitimate business associates or vendors.
This form of fraud relies on a contrived pretext to request a payment or purchase be made on the attacker’s behalf. According to the FBI, BEC attacks resulted in more than $26 billion (you read that right) between June 2016 and July 2019. Here are a few tips for protecting users and businesses from BEC attacks:
Slow down – BEC attacks combine context and familiarity (an email from your boss) with a sense of urgency (I need this done now!). This causes victims to lose their critical thinking capabilities.
Don’t trust, verify – Never use the same channel, in this case email, to verify the identity of the requester. Pick up the phone and call, or use video chat.
Prepare for the inevitable – Use all the technology at your disposal to ensure a BEC attack doesn’t succeed. Machine learning-enabled endpoint security solutions can help identify malicious sites.
Address the weakest link – Train users to spot BEC attacks. Webroot testing shows that phishing simulations can improve users’ abilities to spot attacks.
Perfecting Your Posture
Webroot Security Intelligence Director, Grayson Milbourne, offers several suggestions that companies can do to increase their security posture. First, he says, “Whenever money is going to be sent somewhere, you should have a two-factor verification process to ensure you’re sending the money to the right person and the right accounts.”
Milbourne is also a big advocate of security awareness training. “You can really understand the security topology of your business with respect to your users’ risk factors,” he says. “So, the engineering team might score one way and the IT department might score another way. This gives you better visibility into which groups within your company are more susceptible to clicking on links in emails that they shouldn’t be clicking.”
With the increase in scams related to the global COVID-19 pandemic, timely and relevant user education is especially critical. “COVID obviously has been a hot topic so far this year, and in the last quarter we added close to 20 new templates from different COVID-related scams we see out in the wild,” Milbourne says.
“When we look at first-time deployment of security awareness training, north of 40% of people are clicking on links,” Milbourne says. “Then, after going through security awareness training a couple of times, we see that number dip below 10%.”
Where to learn more
Our newest research on phishing attacks and user (over)confidence, “COVID-19 Clicks: How Phishing Capitalized on a Global Crisis” is out now, check it out!
Cyber News Rundown: Global Cybercrime Costs Surpass $1 Trillion
Cybercrime surpasses $1Trillion in global costs
A recent study has put the global cost of cybercrime at over $1 trillion for 2020. This figure is up significantly from 2018, which was calculated at around $600 billion. And while most effects are financial, roughly 92% of affected organizations cited by the study reported additional issues stemming from cyberattacks. Over half took no measures to prevent or recover from common types of attack.
Major hosting provider affected by cyberattack
The worldwide hosting service provider Netgain was forced to take many of its servers and data centers offline following a recent ransomware incident. The attack occurred just before Thanksgiving and continues to cause intermittent outages for customers as the company works to restore their systems. Due to the volume of systems Netgain provides services for, they remain unsure how long customers will be inconvenienced by the fallout from this attack.
Default passwords compromising radiology equipment
Researchers have discovered that GE has implemented default passwords that can be easily found online across a wide range of medical equipment. These passwords, used by technicians to perform routine maintenance, could also be used illicitly to take control of the machines or cause them to malfunction. Users are unable to change these credentials on their own and require a certified GE tech to come to make on-site adjustments. While GE has stated it does not believe any unauthorized access has been identified, the critical nature of these machines makes this a high priority vulnerability.
Educational technology still lacking proper security
An alarming number of schools and educational institutions switching to remote learning have made no changes to their security policies or implemented any cybersecurity training for staff and/or students. Additionally, nearly 40 percent of the schools surveyed weren’t even able to provide devices for their employees or students to work remotely during the pandemic, though 70 percent had switched their regular communications to video conferencing services.
Payment card skimmers hiding in CSS
Camouflaging payment card skimmers into the CSS of compromised e-commerce site is the latest evasion tactic being used by cybercriminals. The skimmer is run by the Magecart group, which is known for successfully evading detection software and innovating to boost longevity on compromised systems. The embedded script launches during the checkout process by redirecting the customer to a new page where it begins stealing information entered into a form.
Cyber News Rundown: Biological Worries Over Malware Attacks
Biological Worries Over Malware Attacks
Researchers have recently unveiled the latest potential victim for malware authors: biological laboratories. By illicitly accessing these facilities, hackers may be able to digitally replace sections of DNA strings, causing unexpected results when biologists go to create or experiment with these compounds. While it is fortunate that this specific targeted attack was simulated in a closed environment, it brought to light the extreme focus that a cyber-attack may be capable of implementing, and the lengths some attackers may go to accomplish their goal.
SMS App Exposes Messages of Millions
Despite the weeks of effort from the developer, GO SMS Pro an instant messaging app with over 100 million users is still suffering from messages being leaked. What originated as a bug has left the messaging app critically flawed for upwards of three months, with no clear signs of resolution, as even new versions of the app have been unable to rectify the problem. The researchers who discovered the flaw were able to view video and picture messages, along with other private messages, due to the URL shortening that occurs when the messages are sent to contacts that don’t have the app installed.
Colorado Health Service Provider Suffers Patient Data Breach
Sometime during the middle of September, the Colorado-based health service provider AspenPointe suffered a data breach that may have compromised the sensitive health information of nearly 300,000 patients. The facility noticed the unauthorized access over a two-week period, but only began notifying patients of the breach in the third week of November. Officials have also confirmed that everything from names to medical history, and other highly sensitive personal information was stolen, though no reports of misuse have yet arisen.
Ransomware Shuts Down Alabama School District
The Huntsville City school district, one of the largest in Alabama, has been forced to close all operations following a ransomware attack that took place as students and staff were returning from Thanksgiving break. District officials worked quickly to take all devices offline, be them computers or smart phones, to stop the spread of the attack. Students were also sent home early, with no firm statement on when classes would resume, as the attack could take them days or weeks to recover from.
Five Arrested in Louisiana Child Crime Sweep
At least 5 individuals have been arrested by the Louisiana Cyber Crime Unit, following an investigation into the online exploitation of children. By tracing IP addresses and even simply viewing social media profiles of all 5 individuals, law enforcement agents have been able to confirm charges of possession or creation of child pornography, thus removing another group of child predators from the general population.
Why Workers Aren’t Confident in their Companies’ Security (and What to Do About it)
According to data from a recent report, only 60% of office workers worldwide believe their company is resilient against cyberattacks. Nearly one in four (23%) admit to not knowing, while nearly one in five (18%) flat-out think it isn’t.
In the anonymous, write-in responses to the survey, many workers agreed that their employers could be doing more to support them and ensure their security. When asked to elaborate on why they didn’t believe their company was resilient against attacks, the most-repeated answers were along the following lines:
- My company has been hacked before.
- My company doesn’t prioritize security/security spend.
- My company’s equipment and software are poorly maintained.
- My company outsources its security, so we have no direct control.
- I still get phishing emails. Our filtering must not be good enough.
These types of responses highlight two things: a general lack of faith in the company’s security and the perception that companies aren’t investing enough in security systems OR their employees. When considered alongside another question from the survey, there seems to be a third factor at play: there is also confusion as to who should be responsible for a company’s cyber resilience in the first place.
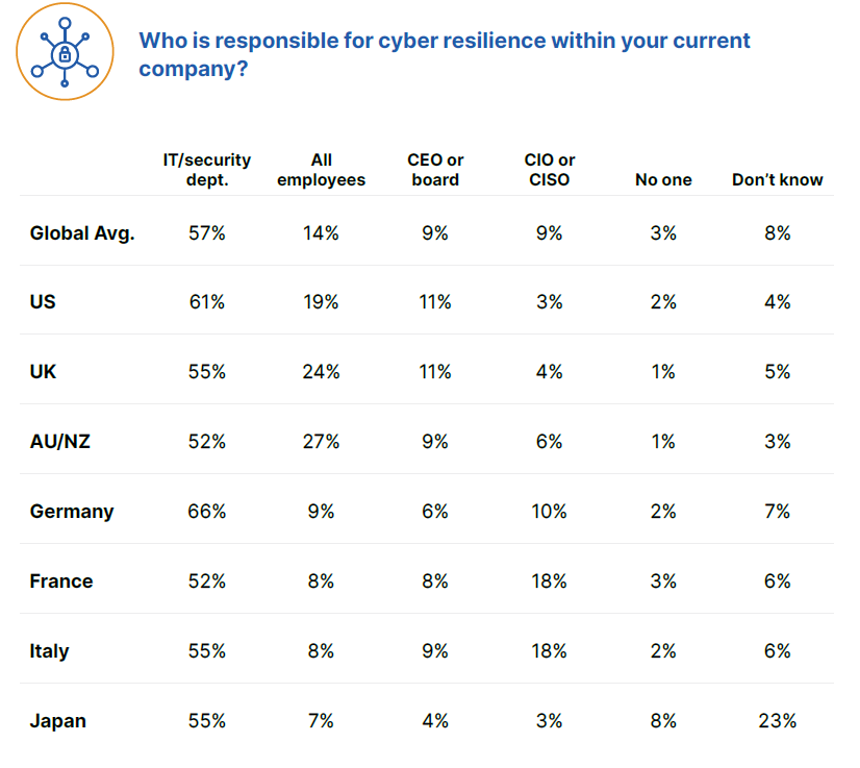
Overall, only 14% of office workers worldwide consider cyber resilience to be a responsibility all employees share. If workers also feel their companies don’t invest enough in them or the tools that protect them, it makes sense that they might not feel like cyber resilience is something they should worry about. If a person feels their employer doesn’t value them appropriately or empower them with the right tools to do their jobs, then the notion of having to expend one’s own time and energy on the company’s security could rankle. So how do you overcome the challenge of personal investment?
How to empower your people and your security
Investment
Dr. Prashanth Rajivan, cybersecurity and human behavior expert, says businesses that want to foster a feeling of personal investment must first tackle the notion of shared responsibility. He explains that, when people perceive themselves to have a greater responsibility to others, their average level of willingness to engage in risky behavior decreases.
“If you’re asking individuals to make changes to their own behavior for the greater safety of all, then you need to make it clear that you are willing to invest in them. By creating a feeling of personal investment in the individuals who make up a company, you encourage the employees to return that feeling of investment toward their workplace. That’s a huge part of ensuring that cybersecurity is part of the culture.” – Prashanth Rajivan, Ph.D.
One way to both empower your workforce to become a strong first line of defense while also demonstrating investment is by implementing a security awareness training program with phishing simulations, as well as giving employees enough time to carefully and thoughtfully complete the learning exercises and understand any applicable feedback.
Consistency
According to Phil Karcher, principal product manager in charge of Webroot® Security Awareness Training, running regular, up-to-date training on an ongoing basis is one of the best ways to help end users avoid attacks and become a strong first line of defense for the company as a whole.
“Data from Webroot® Security Awareness Training shows that, if you want people to make lasting changes to their behavior, you have to run consistent, relevant training courses and phishing simulations that are also varied enough that people won’t get bored or find them predictable. Running a second simulation makes a dramatic impact — and it only gets better from there.”
– Philipp Karcher, principal product manager, Carbonite + Webroot, OpenText Companies
| Number of Phishing Simulations | Click-through Rate |
| 1 | 11% |
| 2-3 | 8% |
| 4-10 | 6% |
| 11-14 | 5% |
| 15-17 | 4% |
Feedback
Dr. Rajivan also reminds us that human behavior is shaped by experience and reinforcement. He and Phil agree that consistency is key for empowering your workforce to become more resilient. But Dr. Rajivan also stresses the importance of feedback over consequences.
“Without appropriate feedback, no amount of training will be effective. And because the average person handles uncertainty poorly, training must include a variety of different scenarios. Human behavior is shaped through varied experiences, with a mix of positive and negative outcomes and applicable feedback.
– Prashanth Rajivan, Ph.D.
This feedback and incentive structure needs to be carefully calibrated. Too much could lead to heightened anxiety and false alarms, but too little could lead to underweighted risk, i.e. people knowing the correct actions, but not taking them.”
Next steps
As phishing attacks continue to be a primary way that businesses get breached, the need for consistent end user education is clear. And by implementing a regular training regimen, you can demonstrate care and investment in your people, educate employees on scams, risks and what to do if the unthinkable happens, and successfully build cyber resilience into your overall company culture.
To take the first step towards cyber resilience and trial an engaging Security Awareness Training program, Take a Free Trial.
Small Businesses are Counting on Their MSPs this Small Business Saturday
This November 28 may be the most important Small Business Saturday since the occasion was founded by American Express in 2010.
As early as July, nearly half (43 percent) of small businesses had closed at least temporarily, according to a study published in the Proceedings of the National Academy of Sciences. Research also suggests that 30 percent of small businesses expect to exhaust their cash on hand before year’s end. Eighty-eight percent have already spent the funds allocated to them by the U.S. government’s Paycheck Protection Program loan.
While hopes will be buoyed for some by recent positive developments in the search for a vaccine, uncertainty and hard times no doubt still lie ahead. That’s why Webroot encourages advocates and partners to shop small this November 28. For our customers, we aim to be a source of support and sound consultation as we recover together.
Challenges and opportunities for small businesses and MSPs
Many of the small businesses affected by COVID-19 are among Webroot’s clientele. Many more, especially managed service providers, count small businesses as their most important customers. We’ve heard from many who are suffering from lost contracts following office closures, fewer onsite projects, disappearing budgets for business development projects and a general slowdown of new business.
Others are witnessing a shift in the work they do and the services most in-demand. For some, COVID-related challenges have presented opportunities to step up and offer services made necessary by new realities. Unsurprisingly, the already trending adoption of cloud infrastructure has quickened its pace in the age of remote work.
“We’ve had to speed up migrating some clients on-premise file servers to online cloud solutions,” according to Russell Harris, a support engineer and project manager at Maya Solutions Ltd., a UK-based MSP specializing in Apple product support
For David Yates, president of Geeks R Us, a West Coast provider of various technical services, the shift to remote work was the push some of his customers needed to leave physical servers behind.
“A few clients who were reluctant to move to the cloud have now embraced it. This was the impetus that they needed to finally migrate away from on-premise servers,” he said.
Many MSPs have also taken it upon themselves to guide their clients through the transition to remote work, especially in terms of security.
“We’ve had to shift to more cloud, VPN and helping our clients work remotely,” says Nathan Hardester, a telecoms administrator with Whidbey Tech Solutions, a Washington-based MSP.
Cybersecurity education is another opportunity for MSPs looking to help small business clients up their cyber resilience. We know that many office workers are overly confident in their ability to detect a phishing attack, so MSPs should position themselves as educators. Already, in the COVID-era, some are finding themselves do exactly that.
Asked what’s changed at Maya Solutions since the pandemic, Harris responds “needing to provide additional training on online safety due to many working from home on their own devices.”
Making it through together
Many MSPs—often small businesses themselves—rely on their small business clients run for their success. And on this Small Business Saturday, small businesses need us all more than ever. Despite the challenges, there are opportunities for MSPs to step up and guide their clients through the changing way we work.
For more tips on staying cyber resilient through COVID-19 and beyond, stay tuned to our Community threat and check out these tips for MSPs looking to help small businesses bounce back.
Cyber News Rundown: REvil Ransomware Strikes
REvil Ransomware Strikes Hosting Provider
In recent days the web hosting provider Managed.com has been working to recover from a ransomware attack targeting many of their core systems. While the company was able to stop the spread of the attack by shutting down their systems and client websites, it remains unclear what information may have been encrypted and sent elsewhere. The demanded ransom is equal to $500,000 in Monero cryptocurrency and is set to double if not paid in the next week.
Cyberattack Shuts Down Americold Operations
Cold storage provider Americold revealed this week it was forced to shut down many of its systems after discovering evidence of a cyberattack. Some variant of ransomware is thought to be responsible for the attack, which has disabled several customer-facing services and could still be affecting Americold. Fortunately, the company responded quickly and was able to stop the attack from spreading across its network, which could have caused significantly more damage, especially if financial information was accessed.
Ticketmaster Receives Fine for 2018 Data Breach
More than two years after Ticketmaster announced a data breach had compromised a significant amount of customer information, the Information Commissioner’s Office (ICO) has settled on a fine of £1.25 million. The attack was significant because, while multiple organizations warned Ticketmaster of the breach, the company did nothing to resolve the security lapse. Officials also discovered that upwards of 60,000 customer payment cards were used for additional fraudulent activity after the Ticketmaster breach.
Healthcare Remains Easiest Target for Cyberattacks
A recent survey of healthcare organizations found that 73% had computer systems totally unprepared to repel a cyberattack. Attackers are improving their operations rapidly compared to security improvements being implemented by these organizations, even with the increasing year-over-year cybersecurity spending. To make matters worse, pressure put on the healthcare industry by the COVID-19 pandemic has forced many facilities to put security improvements on hold as they deal with increased patient numbers.
Severity of Capcom Breach Continues to Rise
A ransomware attack on Capcom that was initially suspected to not affect customer data has been found to be more severe than first thought. Upwards of 135,000 customers, employees and other individuals with ties to the company may have had sensitive personal information compromised. While Capcom has confirmed that payment data is processed through a third-party and isn’t stored on their systems, internal documents and statements seem to have been compromised by the attack.
6 Tips for a More Cyber-Secure Holiday Season
In any other year, many of us would be gearing up for airline travel, big family dinners, cocktail hours or potlucks with friends, and much more. But with all the challenges this year has brought in terms of how we work and connect during a global pandemic, I’m guessing all our plans look a little different than we thought they would.
Since most of us are now online more than ever before for work, school, personal connection, shopping, etc., it’s critical that take extra steps to keep our digital selves safe. With that in mind, we’ve put together a list of 6 (ish) tips to help you and your family stay safe online this holiday season, no matter how or where you celebrate it.
1. Watch out for an increase in scam emails and websites
What follows are just a few of the ways scammers may target you this holiday season. We recommend you install easy-to-use tools such as Fakespot, which is an add-on that protects consumers by detecting fraudulent product reviews and third-party sellers in real time, to help you avoid the fakes.
- Flash sale alerts
During the holidays, the number of promotional emails you receive is likely to go up as online stores run flash sales. With that in mind, scammers are likely to up their game, mimicking legitimate offer emails and websites in the hopes that your desire for a sweet deal will pay out for them. Use extra caution and don’t click anything in an offer email. Go to the retailer’s official website (type it directly into your browser instead of clicking a link in an email) to help ensure you’re shopping securely. - “Free” gift cards
You may get offers for “free” gift cards to online retailers, such as Amazon, Walmart or Target. Remember: very little in life is free. This is another way that criminals may try to trick you into downloading malware or exposing sensitive information that they can use to steal your money or identity. - Fake “missed delivery” notices
Since 94% of people are shopping online more or about the same as they were pre-pandemic, fake package notifications are another way that cybercriminals may target you. If you receive an email or text message about a missed delivery, be sure to double-check the details, such as the shipper (for example, maybe you’re only expecting a Prime or USPS delivery, so a FedEx notification should throw a red flag), the tracking numbers, etc. And, of course, don’t click or download anything in the text or email message itself - Discounts so deep they can’t be real
If you see an ad or email for a high-ticket item that suddenly costs less than 10% of the regular retail price, it’s practically guaranteed to be 100% fake. Let’s face it: there’s just no way you’re going to get real Ray-Bans for the low, low price of $24.99.
2. Use caution with your charitable donations
It’s the giving season and, thanks to the pandemic, natural disasters, and other current events, there are plenty of people in the world who could use a little extra help. Good on you for contributing to the public good! Unfortunately, not even charities are sacred to scammers, and they will take advantage of your desire to help others.
It’s critical to do your research! We recommend you visit trusted organizations, like Charity Watch, to learn more about the charities you’ve chosen and their efficiency, governance and accountability before committing money. Additionally, be suspicious of aggressive pitches including multiple calls and emails or tactics that require immediate donation. Lastly, never pay by gift card of wire transfer. Use a credit card instead, as it’s easier to track and recover fraudulent transactions.
3. Research your smart devices
When we say “smart devices,” we don’t just mean things like Alexa or Google Home. There are internet-enabled fridges that tell you when you’re low on groceries, let you hear and speak to someone at your front door, function as a baby monitor, and even tell you when your laundry’s done. There are also smart thermostats, garage door openers, light fixtures, and so much more. All of these gadgets form a network of connected devices known as the Internet of Things (IoT). And each one could potentially let a hacker into your home network.
Be selective when it comes to purchasing connected smart home and IoT devices. Choose reputable brands that include security, such as the ability to change passwords and perform firmware updates. Cheaper knockoffs of name brand devices might be easier on your wallet, but they are often designed without security in mind. Additionally, since the business model for knockoffs is typically to turn a profit as quickly as possible, there’s no guarantee the device manufacturer will even be around in a year or two to send out security updates or offer support if your device malfunctions
4. Secure any new tech toys right away
Get a cool new gadget in the family gift swap? (Or buy something awesome just for yourself? Don’t worry, we won’t tell the kids.) Protect that tech investment by installing security right away. It’s not the most exciting thing to do with a new toy, but it’ll help make sure you get to enjoy it without worrying about malicious actors joining in on the fun
5. Use reputable video chatting services to connect with loved ones
When planning your virtual holiday get-togethers, use trusted video conferencing providers like Zoom, who have paid close attention to security issues this year and adapted product defaults to enable safer user experiences. Also, be cautious of any websites that request permissions from your browser to access your camera and microphone. If you get one of these notifications, close out of your browser. Do not engage with the permissions request in any way
6. Remember the basics
We’ve said it before, we’ll say it again. Good online habits are your best defense – and it really doesn’t take much effort to keep yourself and your family safe
- Use strong, unique passwords for all your accounts and don’t share them. Length is strength, so passphrases are a good help.
- Install virus protection on all your devices and keep it up to date.
- Use a secure cloud backup.
- Connect to the internet using a VPN, even on your home network (and especially if transmitting sensitive info, like credit card numbers or online banking details.)
- Keep your device operating systems up to date so you have the latest patches against exploits.
- Don’t enable macros. Ever. If a document or website asks you to enable macros or hidden content or “allow access”, just don’t do it. There are very few legitimate reasons for documents or websites to request these permissions.
- Keep a close eye on your financial accounts and look out for any fraudulent activity.
Here’s wishing you a safe and cyber-secure holiday season! Keep an eye on the Webroot Blog and the Webroot Community for more tips and news on the latest cyber threats.
What’s the deal with security product testing anyway?
It’s common for savvy online shoppers to check third-party reviews before making an online purchasing decision. That’s smart, but testing the efficacy of security software can be a bit more difficult than determining if a restaurant had decent service or if clothing brand’s products are true to size.
So, with the arguably more significant consequences of antimalware testing, how can shoppers be sure that the product they choose is up to the task of protecting their family from malware? Which reviews are worthy of trust and which are just fluff?
Red flags in antimalware testing
Grayson Milbourne is the security intelligence director at Webroot and actively involved in improving the fairness and reliability of antimalware testing. While acknowledging that determining the trustworthiness of any single test is difficult, some factors should sound alarm bells when looking to honestly evaluate antimalware products.
These include:
The pay-to-perform model
In any test, the humans behind the product being evaluated have a vested interest in the performance. How far they go to influence those results, however, varies. One extreme way to positively influence results is to fund a test designed for your product to succeed. Often, the platform on which a test appears can be a sign of whether this is the case.
“YouTube tests are almost always commissioned,” warns Milbourne. “So, if you see things on YouTube, know that there is almost always someone paying for the test who’s working the way the test comes out. I try to avoid those.”
If only one product aces a test, that’s another sign that it may have been designed unfairly, maybe with the undisputed winner’s strengths in mind.
Every vendor acing a test
Tests in which all participants receive high scores can be useless in evaluating product efficacy. Because we know catching malware is difficult, and no single product is capable of doing it effectively 100 percent of the time, tests where every product excels are cause for concern.
“If every product aces the test, maybe that test is a little too easy,” says Milbourne. No product is perfect, so be wary of results that suggest so.
Failing to test in “the big picture”
No one piece of software can stop all the threats a user may face all of the time. But many vendors layer their preventative technologies—like network, endpoint and user-level protection—to most effectively protect against cyberthreats.
“Testers are still very worried about what happens when you encounter a specific piece of malware,” says Milbourne. “But there’s a lot of technology focused on preventing that encounter, and reactive technology that can limit what malware can do, if it’s still unknown, to prevent a compromise.”
In addition to how well a product protects an endpoint from malware, it’s also important to test preventative layers of protection which is lacking in 3rd party testing today.
The problem with the antimalware testing ecosystem
For Milbourne, the fact that so few organizations dedicated to efficacy testing exist, while the number of vendors continues to grow, is problematic.
“There are about five well-established third-party testers and another five emerging players,” he says. But there are well over a hundred endpoint security players and that number is growing.”
These lopsided numbers can mean that innovation in testing is unable to keep up with both innovation in security products as well as the everchanging tactics used by hackers and malware authors to distribute their threats. Testing organizations are simply unable to match the realities of actual conditions “out in the wild.”
“When security testing was first being developed in the early 2000s, many of the security products were almost identical to one another,” says Milbourne. “So, testers were able to create and define a methodology that fit almost every product. But today, products are very different from each other in terms of the strategies they take to protect endpoints, so it’s more difficult to create a single methodology for testing every endpoint product.”
Maintaining relationships in such a small circle was also problematic. Personal relationships could easily be endangered by a bad test score, and a shortage of talent meant that vendors and testers could bounce between these different “sides of the aisle” with some frequency.
Recognizing this problem in 2008, antimalware vendors and testing companies came together to create an organization dedicated to standardizing testing criteria, so no vendor is taken off guard by the performance metrics tested.
The Anti-Malware Testing Standards Organization (AMTSO) describes itself as “an international non-profit association that focuses on addressing the global need for improvement in the objectivity, quality and relevance of anti-malware testing methodologies.”
Today, its members include a number of antivirus and endpoint security vendors and testers, normally in competition against one another, but here collaborating in the interest of developing more transparent and reliable testing standards to further the fair evaluation of security products.
“Basically, the organization was founded to answer questions about how you test a product fairly,” says Milbourne.
Cutting through the antimalware testing hype
Reputation within the industry may be the single most important determinant of a performance test’s trustworthiness. The AMTSO, which has been working towards its mission for more than a decade now, is a prime example. Its members include some of the most trusted names in internet security and its board of directors and advisory board are made up of seasoned industry professionals who have spent entire careers building their reputations.
While none of this is to say there can’t be new and innovative testing organizations hitting the scene, there’s simply no substitute for paying dues.
“There are definitely some new and emerging testers which I’ve been engaging with and am happy to see new methodologies and creativity come into play, says Milbourne, “but it does take some time to build up a reputation within the industry.”
For vendors, testing criteria should be clearly communicated, and performance expectations plainly laid out in advance. Being asked to hit an invisible target is neither reasonable nor fair.
“Every organization should have the chance to look at and provide feedback on a tests’ methodology because malware is not a trivial thing to test and no two security products are exactly alike. Careful review of how a test is meant to take place is crucial for understanding the results.”
Ultimately, the most accurate evaluation of any antimalware product will be informed by multiple sources. Like reviews are considered in aggregate for almost any other product, customers should take a mental average of all the trustworthy reviews they’re able to find when making a purchasing decision.
“Any one test is just one test,” reminds Milbourne. “We know testing is far from perfect and we also know products are far from perfect. So, my advice would be not to put too much stock into any one test, but to look at a couple of different opinions and determine which solution or set of solutions will strengthen your overall cyber resilience.”
Cyber News Rundown: Flood of Phony IRS Emails
Phony IRS Emails Flooding Inboxes
Upwards of 70,000 inboxes have been receiving spam claiming to be from the IRS threatening legal action for late or missing payments. Most recipients are Microsoft Office 365 users and have been receiving threats of lawsuits to, wage garnishment and even arrest. These spoofing scams have risen in popularity in recent years, but have mixed results since many users are familiar with the tactic.
Pakistani Airlines Network Access for Sale
Researchers found a listing for full admin access to the Pakistan International Airlines network on multiple dark web forums earlier this week. The current asking price is an incredibly low $4,000, considering the amount of information that could be used for malicious activities. The hackers claim to have 15 databases, each with many thousands of records, including passport data and other highly sensitive personal information on passengers and employees alike. It is believed that this group has been responsible for at least 38 other sales of network access in the past five months.
Zoom Enhances Security at Heed of FTC
Following a settlement with the FTC, the video communication service Zoom is being forced to upgrade its overall security after it was found that they weren’t implementing the end-to-end encryption the business touted. It was also discovered that encryption of recorded video calls often did not take place and regular security testing of security measures did not occur, endangering user privacy for personal video calls and chats.
Mashable Database Compromised
The online media outlet Mashable confirmed it had suffered a cyberattack on its systems, and that the attacker had already published some of the stolen data, this weekend. Fortunately, Mashable also confirmed the stolen data was from a system that was no longer in use. The company has also begun contacted affected customers and informing them to be wary of suspicious emails and to forward them to Mashable for further investigation.
Millions of RedDoorz Records for Sale
Roughly 5.8 million user records belonging to the hotel booking platform RedDoorz were found for sale on a hacker forum. These records were likely the the result of a cyberattack targeting RedDoorz in September, though the company firmly stated no financial information was compromised. After viewing a sample of the stolen data, however, it was discovered that a significant amount of extremely sensitive information belonging to customers who may have stayed at any of their 1,000 properties across Southeast Asia had been published.
Employee Spotlight: From Building Code to Building Teams
Webroot is a dynamic team of hard-working individuals with diverse backgrounds. One of those hard-working individuals is Ben Jackson, Senior Manager of Software Development, Engineering. Ben started off building pages in HTML. Now he leads high-performing teams and helps develop architectures from his home in the UK. We sat down with Ben to find out how he got into software and where he sees the biggest growth opportunities.
What were you doing before working at Webroot?
I worked at a Smart Meter manufacturer in the UK on their manufacturing systems and had a short stint at a big UK retailer called Next working on their retail website.
What brought you to Webroot?
The opportunity to work on some really cool tech, and the people and culture really attracted me.
What is your role in the company?
I am a Senior Software Development Manager for the Sky Services and Efficacy tools.
How did you get into software development?
I took a shine to it from an early age when I was trying to find something to do for a career back at school. I started with the most basic HTML web page in my spare time by copying the code from a textbook into notepad and saving it as an html file to see it run. I have never looked back.
What are the primary coding languages you specialize in?
Microsoft .net framework technologies with languages such as C#. I can use Visual Basic but I’m not a huge fan, and also Java.
What are the advantages of those languages and how do they manifest themselves in your work?
C# is in the core of what we do as a team. All our applications are in the Microsoft .net framework stack, and through the use of .net core in a lot of our new projects, we can run our code on any operating system, making it very easy to deploy, such as in Linux or Docker containers.
What parts of your job require you to think outside of strictly writing code, for example, system architecture, use cases, etc.?
Most of my job requires me to think outside of writing code, especially working with other engineering teams, product management, and helping design the architecture of some of our decoupled systems.
What are your proudest accomplishments as a software engineer?
I have contributed to and led numerous software projects in my career that I am very proud of, but my proudest achievements are in building teams that work together to deliver something special and noteworthy in terms of how the team collaborated together, especially my current team.
Where do you think the future of software development is headed?
It is tricky to say as direction changes all the time and people have such differing opinions, but I feel it will certainly be the continuation of the cloud (Amazon Web Services, Microsoft Azure and Google Cloud) being king. The management of the infrastructure to run applications will further be detached from the developer so that they will just be writing the code and handing it over to the cloud to deploy, scale and manage for you automatically. Serverless architectures will become more of the norm, I think.
War Games or The Matrix?
War Games! It was released the year before I was born, but I have grown up with it through watching re-runs.
What else do you like to do besides coding?
I am a big football (soccer) and sports fan and try to watch as much as I can. I used to play 11-a-side football as a goalkeeper every Saturday for a local team until my recent retirement to spend more time with my two children, who are my biggest focus now outside of work.
Any personal details or stories you’d like to share?
I once appeared on a Portuguese news channel while at a friend’s stag (bachelor party). I was dressed as a pirate, doing the iconic scene from the film Titanic at the front of a fishing boat as it came into the harbor. For some reason, a news crew interviewed us and ran it on the early evening news with the Titanic theme song by Celine Dion playing in the background. I have no idea why they found us so interesting!
Want to find out about job opportunities at Webroot? Visit our careers page.
Getting to Know Cloudjacking and Cloud Mining Could Save Your Business
A few years back, cryptojacking and cryptomining emerged as relatively low-effort ways to profit by hijacking another’s computing resources. Today, cloudjacking and cloud mining capitalize on similar principles, only by targeting the near infinite resources of the cloud to generate revenue for attackers. Knowing this growing threat is key to maintaining cyber resilience.
Enterprise-level organizations make especially attractive cloudjacking targets for a few reasons. As mentioned, the computing power of cloud networks is effectively limitless for all but the most brazen cybercriminals.
Additionally, excess electricity consumption, one of the most common tipoffs for smaller scale cryptojacking attacks, often goes unnoticed at the scale large corporations are used to operating. The same goes for CPU.
Careful threat actors can also throttle back the amount of resources they’re ripping off—when attacking a smaller organization, for instance—to avoid detection. Essentially, the resources stolen at any one time in these attacks are a drop in the Pacific Ocean to their largest targets. Over time, though, and depending on particulars of a usage contract, the spend for CPU used can really add up.
“Hackers have definitely transitioned away from launching ransomware attacks indiscriminately,” says Webroot threat analyst Tyler Moffitt. “It used to be, ‘everybody gets the same payload, everyone has the same flat-rate ransom.’
“That’s all changed. Now, ransomware actors want to go after businesses with large attack surfaces and more pocketbook money than, say, grandma’s computer to pay if they’re breached. Cloud is essentially a new market.”
High-profile cloudjacking incidents
Arguably the most famous example of cloudjacking, at least in terms of headlines generated, was a 2018 attack on the electric car manufacturers Tesla. In that incident, cybercriminals were discovered running malware to leech the company’s Amazon Web Service cloud computing power to mine cryptocurrency.
Even with an organization of Tesla’s scale, the attackers reportedly used a throttling technique to ensure their operations weren’t uncovered. Ultimately, they were reported by a third-party that was compensated for their discovery.
More recently, the hacking group TeamTNT developed a worm capable of stealing AWS credentials and implanting cloudjacking malware on systems using the cloud service. It does this by searching for accounts using popular development tools, like Docker or Kubernets, that are both improperly configured and running AWS, then performing a few simple searches for the unencrypted credentials.
TeamTNT’s total haul remains unclear, since it can spread it’s ‘earnings’ across multiple crypto wallets. The fear though, now that a proven tactic for lifting AWS credentials is out in the wild, is that misconfigured cloud accounts will become prime targets for widespread illicit cloud mining.
SMBs make attractive targets, too
Hackers aren’t just launching cloudjacking attacks specifically against storage systems and development tools. As with other attack tactics, they often see MSPs and small and medium-sized businesses (SMBs) as attractive targets as well.
“Several attacks in the first and second quarters of 2019 involved bad actors hijacking multiple managed service providers,” says Moffitt. “We saw that with Sodonakibi and GrandCrab. The same principles apply here. Hacking a central, cloud-based property allows attackers to hit dozens and potentially hundreds of victims all at once.”
Because smaller businesses typically share their cloud infrastructure with other small businesses, compromising cloud infrastructure can provide cybercriminals with a trove of data belonging to several concerned owners.
“The cloud offers an attractive aggregation point as it allows attackers access to a much larger concentration of victims. Gaining access to a single Amazon web server, for instance, could allow threat actors to steal and encrypt data belonging to dozens of companies renting space on that server hostage,” says Moffitt.
High-value targets include confidential information like mission-critical data, trade secrets, unencrypted tax information or customer information that, if released, would violate privacy laws like GDPR and CCPA.
Some years ago, smaller businesses may have escaped these cloud compromises without too much disruption. Today, the data and services stored or run through the cloud are critical to the day-to-day even for SMBs. Many businesses would be simply crippled should they lost access to public or private cloud assets.
The pressure to pay a ransom, therefore, is significantly higher than it was even three years ago. But ransoms aren’t the only way for malicious actors to monetize their efforts. With cloud mining, they can get right to work making cryptocurrency while evading notice for as long as possible.
How to protect against cloudjacking and cloud mining
Moffitt recommends using “versioning” to guard against cloudjacking attacks. Versioning is the practice of serializing unalterable backups to prevent them from being deleted or manipulated.
“That means not just having snapshot or history copies—that’s pretty standard—since with ransomware we’ve seen actors encrypt all of those copies. So, my suggestion is creating immutable backups. It’s called versioning, but these are essentially snapshot copies that can never be edited or encrypted.”
Moffitt says many service providers have this capability, but it may not be the default and need to be switched on manually.
Two more tactics to adopt to defend against cloud jacking involve monitoring your configurations and monitor your network traffic. As we’ve seen, capitalizing on misconfigured AWS infrastructure is one of the more common ways for cybercriminals to disrupt cloud services.
Security oversight of devops teams setting up cloud applications is crucial. There are tools available that can automatically discover resources as soon as they’re created, determine the applications running on the resource and apply appropriate policies based on the resource type.
By monitoring network traffic and correlating it with configuration data, companies are able to spot suspicious network traffic being generated as they send work or hashes to public mining pools that are public and could help identify where mining is being directed.
There tends to be a learning curve when defending against emerging attacks. But if businesses are aware of how cloud resources are manipulated by threat actors, they can be on guard against cloudjacking by taking a few simple steps, increasing their overall cyber resilience.
Cyber News Rundown: Maze Ransomware Shuts Down
Maze Ransomware Group Ends Operations
A press release issued this week announced the end of the Maze ransomware group’s data theft operations. In the release, the Maze authors revealed their motives behind one of the most successful ransomware campaigns to date, and why they chose to finally shut down their massive project. It also stated the Maze team was working to expose the major security holes key industries fail to address, though their methods created many victims.
Magecart Targets International Gold Retailer
Nearly three months after a data breach caused by a Magecart attack struck the international precious metals retailer, JM Bullion has finally released an official statement to customers. After identifying unauthorized activity on their systems in the mid-July, the company went on to find that their systems had been compromised since February by Magecart payment card-skimming software. The company has yet to acknowledge why took so long to discover the breach or why it failed to follow GDPR regulations by immediately contacting affected customers.
Ryuk Remains Top Player Throughout 2020
With ransomware continuing its stay at the top of the cyberthreat throne, Ryuk variants have been responsible for over a third of all ransomware attacks in 2020 alone or roughly 67 million attacks. Ryuk has been around for over two years, but found much greater success this year after being found responsible for only 5,100 attacks in 2019. Ransomware attacks grew 40 percent over last year, to nearly 200 million as of Q3.
Cannabis Site Leaves Database Exposed
An unsecured database belonging to cannabis website GrowDiaries and housing over 3.4 million user records was found to be accessible last month. The data included 1.4 million user passwords that were encrypted using MD5 hashing, which is known to be easily unlocked by cybercriminals. Nearly a week after being informed of the database GrowDiaries properly secured it from public access, though it remains unclear how long it was accessible or who accessed it during that time.
Mattel Reveals Ransomware Attack
Following a July ransomware attack, Mattel has finally issued an official statement regarding the overall damage. The company has confirmed that no data was stolen during the attack, which was quickly identified by their security, and many systems were taken offline to prevent any damage or theft occured. The ransomware attack was likely perpetrated by TrickBot, as it’s known for concentrating on large organizations and leaving them exposed for some encrypting variant to follow.